Matching process settings
You can manage the matching process settings by selecting the Settings tab and then the Matching tab.
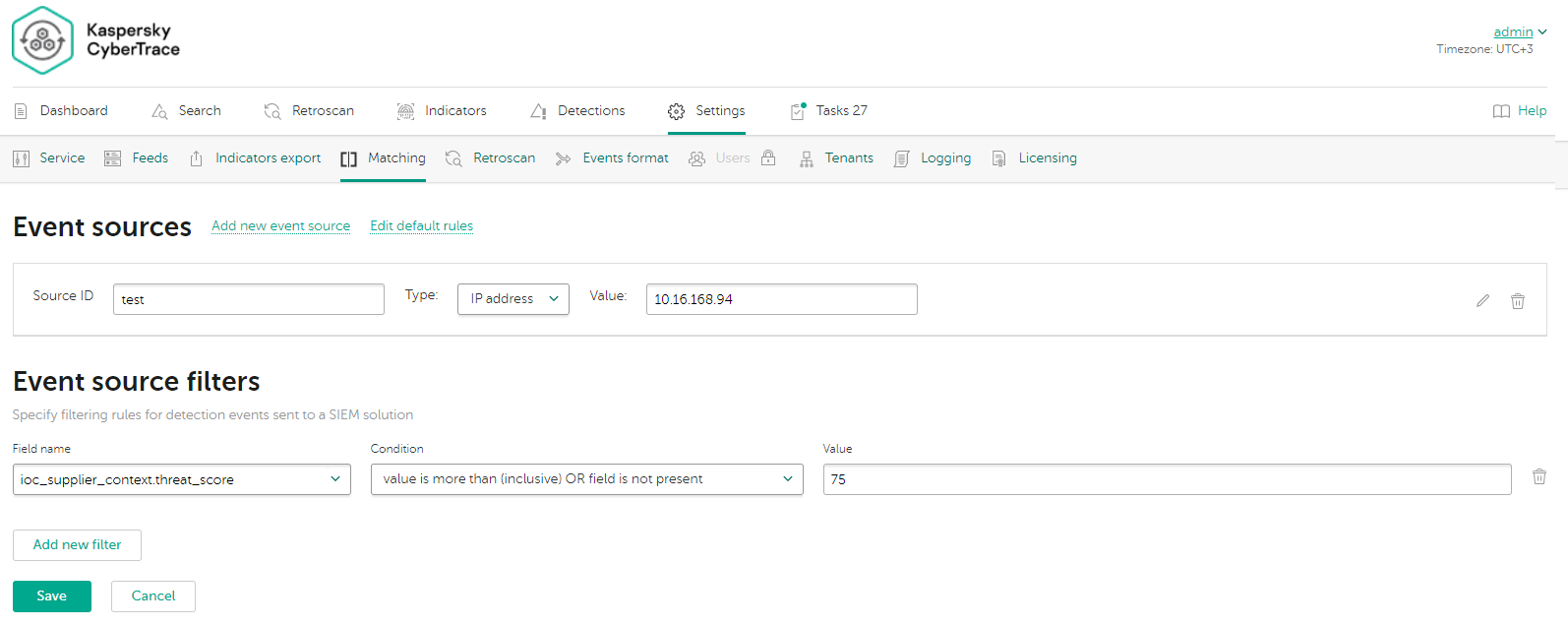
Event sources
In Kaspersky CyberTrace, regular expressions and event normalization rules are grouped by event source. Regular expressions and event normalization rules that are not related to a specific event source are grouped under the default event source. Each event source must have at least one regular expression. You can add or remove event sources other than default or edit their properties.
The Event sources page displays all event sources defined in the Kaspersky CyberTrace Service configuration file, except the default event source. You can edit the following properties of the displayed event sources directly in the Event sources page:
- Source ID
The name of the event source. It must be unique among the event source names used. In the name the following symbols are allowed: Latin letters, numbers, a hyphen (
-), a period (.), and an underscore (_). - Event source type
You can select one of the following options:
- IP address
The IP address of a device that issues events for which you want to add parsing rules. Both IPv4 and IPv6 addresses are supported.
- Host name
The host name of a device that issues events. The value must be the same as the value in the
HOSTNAMEfield of the incoming syslog messages from this event source. - Regular expression
The regular expression that will match the source in the events received by Kaspersky CyberTrace. This regular expression must be optimized. For more information on how to optimize regular expressions, see the "Optimization of regular expressions" subsection of the "About regular expressions" section.
- IP address
To edit the event normalization rules and regular expressions defined for a displayed event source, select the corresponding Properties link. For the default event source, you must select the Edit default rules link. In both cases, the form for editing event source properties opens (see subsection "Form for editing event source properties" below).
For more information on event sources and regular expressions used for parsing events that are issued by various devices, see section "About regular expressions".
Adding event sources
To add an event source:
- Select the Add new event source link.
The Add New Event Source Wizard starts.
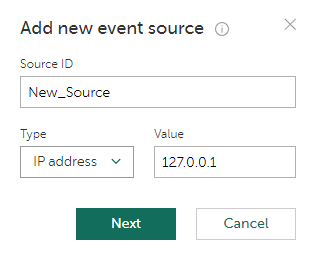
Adding a new event source (step 1)
- Specify the name and the IP address or host name or the regular expression of a new event source.
Both IPv4 and IPv6 addresses are supported.
- Click Next.
If the data entered at the previous step is correct, the form for specifying regular expressions and event normalization rules opens (see subsection "Form for editing event source properties" below).
Kaspersky CyberTrace will attempt to obtain data from received events by using the default regular expressions. We recommend that you keep collecting events for at least five seconds.
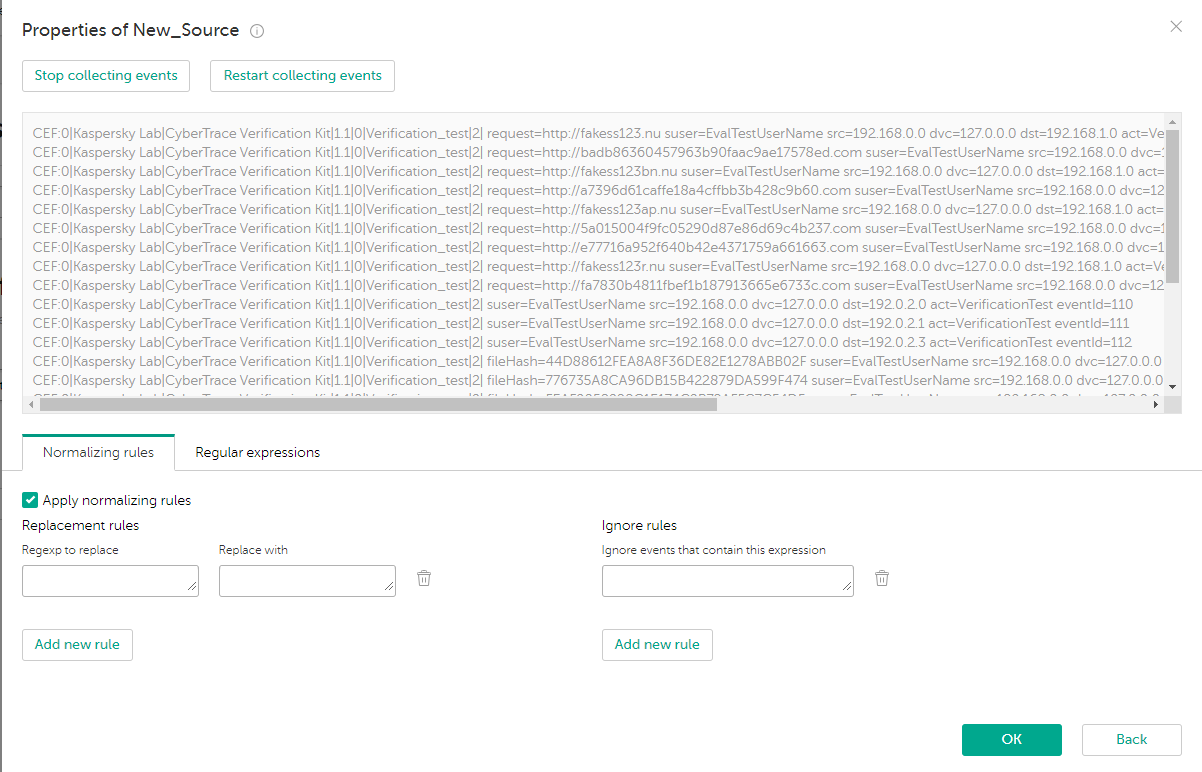
Specifying the event source properties
- Specify the event source properties and click OK.
If the entered event source properties are correct, a new event source is created.
Form for editing event source properties
The form for editing event source properties has an upper area and the lower area. The upper area displays events and highlights substrings that are extracted by a selected regular expression. The lower area has two tabs: the Normalizing rules tab and the Regular expressions tab.
When the form for editing event source properties opens, it starts collecting events that are issued by the event source. These events are processed according to the normalization rules and the result is displayed in the upper area of the form.
If you have specified the host name of the event source, but the HOSTNAME field of incoming events cannot be extracted, no event is displayed. To fix this problem, either specify the IP address or regular expression of the event source, or change the format of events.
You can pause (or resume), or restart collecting the arriving events in real time. If you restart collecting the incoming events, the text box for displaying events is cleared. This text box can contain up to 50 lines. If more data arrives, older data is removed.
Specifying event normalization rules
In the lower area of the form for editing event source properties, select the Normalizing rules tab to add, remove, or edit normalization rules that will be applied to incoming events that meet the conditions of the event source. You can specify which character sequences must be replaced with others (replacing rules) and which character sequences must be used for identifying events to ignore (ignoring rules). If you clear the Apply normalizing rules check box, all the controls for specifying normalization rules will be disabled, and no normalization rule will be saved for the event source being edited.
Do not specify the newline character (\n) in replacing rules. Use the InputSettings > EventDelimiter element of the Kaspersky CyberTrace Service configuration file to separate compound incoming events into individual events.
For an event source that is being created, initially the form under the Normalizing rules tab is filled with the normalization rules specified for the default event source.
Specifying regular expressions
In the lower area of the form for editing event source properties, select the Regular expressions tab to add, remove, or edit regular expressions that will be applied to incoming events that meet the conditions of the event source. For an event source that is being created, initially the form under the Regular expressions tab is filled with the regular expressions that are specified for the default event source and that extract at least some data from the events that are displayed.
Regular expressions have the following properties:
- Indicator type
The type of data to be extracted from an event. You can set one of the following indicator types:
- URL
- MD5
- SHA1
- SHA256
- HASH
- IP
- DOMAIN
- CONTEXT
- Regular expression name
The regular expression name must be unique among the names of the regular expressions that relate to the same event source.
- Regular expression itself
The regular expression used for extracting the required value from an event. For more information on regular expressions, see section "About regular expressions".
- Extract all check box
If this check box is cleared, the regular expression will extract only the first matched value. If this check box is selected, the regular expression will extract all of the matched values.
- Concatenation rules
You can specify how to concatenate different parts of extracted data to a single value. For information about concatenation of extracted data, see section "About regular expressions", subsection "Compound values".
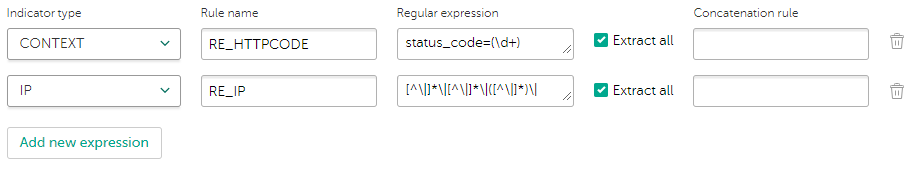
Setting regular expressions and their properties
You can highlight values that match the regular expressions that you specified for the event source. Click inside the text box that contains the regular expression that you want to highlight.
Specifying event filters
You can specify filtering rules for detection events sent to a SIEM system from Kaspersky CyberTrace. Kaspersky CyberTrace will send detection events only if the flag for sending detection events to the SIEM system (the ioc_supplier_send_match event attribute from the indicator database) is set to true and all fields of a feed record that matched the indicator meet the filtering criteria. Note that if the detected indicator does not have the attribute specified in the filtering rule, this indicator is considered to meet the filter. However, all detection events will be included in statistics and displayed on the Dashboard and Detections tabs.
To specify filters for detection events:
- In the Field name drop-down list, select the value corresponds to the indicator attribute name from the indicator database to which filtering rules are applied.
To learn more about possible values for
%FIELD_NAME%, see section "Working with indicators". - In the Condition drop-down list, select a filtering condition.
For the list of possible filtering conditions, see section "About filtering criteria for sending events to SIEM".
- In the Value text box, specify a filtering value.
Do not use a semicolon ('
;') to separate values in this text box. Instead, select value is one of (separated by a new line) in the Condition drop-down list and use a newline character ('\n') or press Enter to separate values. Otherwise, the filter will not be applied correctly. - Click the Add new filter button if you want to add new event filter.
If necessary, you can edit or delete any filtering rules.
Page top