About the single-instance integration scheme
By default, both Kaspersky CyberTrace Service and Kaspersky CyberTrace App use the following integration scheme. This scheme is the single-instance integration scheme.
About apps and services
The single instance integration scheme uses one app and one service:
- Kaspersky CyberTrace Service
This service matches Splunk events against Kaspersky Threat Data Feeds.
Kaspersky CyberTrace Service sends the resulting alerts to Splunk. Splunk stores the alerts from Kaspersky CyberTrace Service in the
mainindex. - Kaspersky CyberTrace App
This app contains Kaspersky CyberTrace App dashboards, alert templates, and a lookup script. The app also contains parsing rules for Kaspersky CyberTrace Service events and rules for forwarding events from Splunk to Kaspersky CyberTrace Service.
Single-instance integration scheme
In the single-instance integration scheme, Splunk Apps and Kaspersky CyberTrace Service work on the same computer by default (IP address is 127.0.0.1). Kaspersky CyberTrace App receives input on port 3000 and forwards it to Kaspersky CyberTrace Service on port 9999. Kaspersky CyberTrace Service then returns matches to Kaspersky CyberTrace App on port 9998.
If you want to install Kaspersky CyberTrace Service on a separate computer, you must specify the addresses and ports used by Kaspersky CyberTrace Service and Kaspersky CyberTrace App when installing Kaspersky CyberTrace.
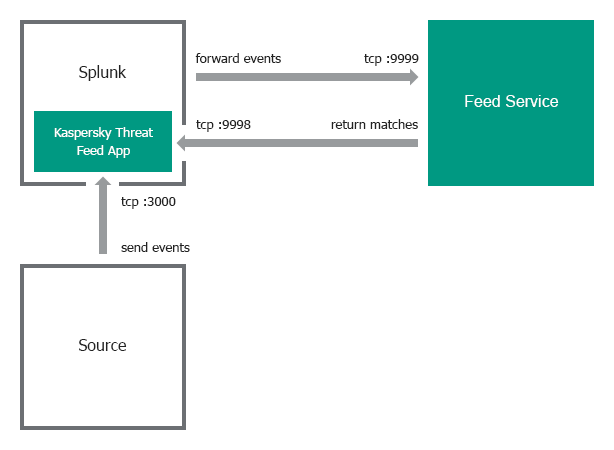
Single-instance integration scheme
Event format
By default, Kaspersky CyberTrace App and Kaspersky CyberTrace Service receive events in a certain format:
- Kaspersky CyberTrace Service uses regular expressions from its configuration file to parse events. You can view and configure these regular expressions on the Settings → Matching tab in Kaspersky CyberTrace Web. These regular expressions parse a specific format of inbound data. For example, the default regular expression for URLs matches strings that contain a protocol (for example,
http://orhttps://). If URLs in the events that come from your devices do not contain protocols, you must change the regular expression. - The lookup script that comes with Kaspersky CyberTrace App sends events to Kaspersky CyberTrace Service in a format that matches the regular expressions used by Kaspersky CyberTrace Service. When you change the regular expressions, edit the lookup script so that it uses a format that matches the new regular expressions.