Contents
- About Kaspersky Anti-Ransomware Tool for Home
- Protection components
- Install and uninstall the application
- Data provision
- Application interface
- Perform common tasks
- Onboarding
- Configure and check the proxy server settings
- Enable notifications
- Set the machine block time
- Types of objects to detect and block
- Block exploits
- Password-protect the application settings
- Exclusions
- Blocked items
- View information on detected objects
- Scan your PC for threats
- Log application events
- Activity report
- Manage the application from the Command Prompt
- Appendix 1. Network settings for interaction with external services
- Get technical support
- Leave feedback
- Information about third-party code
- Trademark notices
- Terms & Conditions
About Kaspersky Anti-Ransomware Tool for Home
Kaspersky Anti-Ransomware Tool for Home is designed to protect against ransomware applications that can, for example, block access to a computer system until a sum of money is paid. Kaspersky Anti-Ransomware Tool for Home also raises user awareness by providing information materials on emerging cyberthreats and protection solutions.
Computer protection
Kaspersky Anti-Ransomware Tool for Home detects malicious applications or legitimate software that can be used to damage your data (adware and others) and automatically blocks suspicious activity. The application stores data areas modified by suspicious processes in the hidden and protected storage. If a suspicious process creates or modifies files or the system registry, Kaspersky Anti-Ransomware Tool for Home detects such changes, blocks the process, and then attempts to roll back the actions of the detected object by restoring the data areas from the protected storage. Kaspersky Anti-Ransomware Tool for Home is equipped with a self-protection mechanism to prevent modification or deletion of its files from the hard drive, memory processes and system registry entries.
Kaspersky doesn't receive any data areas that are used by the application to roll back the actions of detected objects.
Detection methods
Kaspersky Anti-Ransomware Tool for Home detects suspicious activity using anti-virus databases and Kaspersky Security Network.
Anti-virus databases provide protection from known threats. Kaspersky Anti-Ransomware Tool for Home compares behavior of applications on the computer with viruses and other malware registered in anti-virus databases. Note that a database update can change security settings that are not available to the user.
Kaspersky Security Network provides protection from the newest threats. Kaspersky Anti-Ransomware Tool for Home automatically sends statistics retrieved from your computer to Kaspersky. Participation in Kaspersky Security Network lets your computer access reputation statistics for applications and websites.
News and special offers
We and our partners now provide you via the application with information materials, for example, about Kaspersky sales or emerging cyberthreats.
In case of receiving the software from a Kaspersky's partner company, the software can be customized. In the customized software, some of the settings or functionality may not be available. You can get more information about the customized software from the partner company.
Hardware and software requirements
General requirements:
- Internet connection (for updating anti-virus databases and application modules; in case if you want to run the installation in silent mode)
Minimum requirements for laptop and desktop computers:
- Free hard drive space: 350 MB (depending on the size of anti-virus databases)
- Processor: Intel Pentium III CPU 1 GHz for 32-bit and 64-bit systems or a compatible equivalent
- RAM: 1 GB for 32-bit operating systems / 2 GB for 64-bit operating systems
Minimum requirements for tablet computers:
- Microsoft Tablet PC
- Processor: Intel Celeron CPU 1.66 GHz
- RAM: 1 GB
Minimum requirements for netbooks:
- Intel Atom CPU 1.60 GHz or faster
- RAM: 1 GB for 32-bit operating systems, 2 GB for 64-bit operating systems
- 10.1-inch display with screen resolution of 1024x600 pixels
- Video card: Intel GMA 950 or a compatible equivalent
Supported operating systems:
- Windows Server 2022 Standard, Enterprise, Datacenter
- Microsoft Windows 11 Enterprise, Pro, Home (21H2, 22H2, 23H2)
- Microsoft Windows 10 Enterprise, Pro, Home (RTM, Threshold 2, Redstone 1, Redstone 2, Redstone 3, Redstone 4, Redstone 5, 19H1, 19H2, 20H1, 20H2, 21H1, 22H2, 23H2), x86/x64
- Microsoft Windows 8.1 Core, Pro, Enterprise (RTM or later), x86/x64
- Microsoft Windows 8 Core, Pro, Enterprise x86/x64
- Microsoft Windows 7 Home Basic, Home Premium, Professional (RTM or later), x86/x64
- Windows Server Standard, Enterprise, Datacenter 2008 R2/2012/2012 R2/2016/2019 19H1/2019 19H2 20H2
Limitations in support of Windows operating system
Supported versions of Windows:
- Microsoft Windows 10 Enterprise (RTM, Threshold 2, Redstone 1, Redstone 2, Redstone 3, Redstone 4, Redstone 5, 22H2), x86/x64
- Microsoft Windows 10 Pro (RTM, Threshold 2, Redstone 1, Redstone 2, Redstone 3, Redstone 4, Redstone 5, 22H2), x86/x64
- Microsoft Windows 10 Home (RTM, Threshold 2, Redstone 1, Redstone 2, Redstone 3, Redstone 4, Redstone 5, 22H2), x86/x64
- Microsoft Windows 8.1 Core (RTM or later)/Pro (RTM or later)/Enterprise (RTM or later), x86/x64
- Microsoft Windows 8 Core/Pro/Enterprise, x86/x64
- Microsoft Windows 7 Home Basic (RTM or later)/Home Premium (RTM or later)/Professional (RTM or later), x86/x64
- Windows Server Standard/Enterprise/Datacenter 2008 R2/2012/2012 R2/2016/2019
Limitations:
- After upgrading from Microsoft Windows 7 to Microsoft Windows 10, you need to reinstall the product to fully support Microsoft Windows 10 21H1 and higher.
- For the Trusted machines feature to work, the Audit logon events function must be enabled in Windows.
- The installation and running of Kaspersky Anti-Ransomware Tool in a Windows Sandbox environment is not supported.
Compatibility with other applications
Compatibility with Kaspersky applications
Kaspersky Anti-Ransomware Tool for Home cannot be installed if you have other Kaspersky antiviruses on your computer. When you install Kaspersky Anti-Ransomware Tool for Home on your computer, the application checks it for other Kaspersky antiviruses. If such applications are detected, Kaspersky Anti-Ransomware Tool for Home interrupts the installation. Compatibility with other Kaspersky applications is not guaranteed.
Upgrading from Kaspersky Anti-Ransomware Tool for Home to Kaspersky Anti-Ransomware Tool for Business and vice versa is not supported. You will need first to uninstall your application.
Compatibility with other anti-virus applications
Kaspersky Anti-Ransomware Tool for Home supports compatibility with most anti-virus applications.
Page top
Limitations and warnings
Kaspersky Anti-Ransomware Tool for Home has the following known limitations:
- In some cases, the application does not delete files that were created by malware.
- The application does not delete or restore files used by another process.
- The application does not protect or restore files located on storage devices that have a file system other than NTFS.
- The application does not restore registry keys created by malware.
- The application does not support EFS-encrypted files.
- When processes or process flows affected by malware are terminated, the operating system might become unstable.
- The application rolls back all file modifications that were made during analysis of a process.
- In some cases, empty folders may remain after the application has been uninstalled.
- In rare cases, the application interface may become unstable if the application is used in multiple user sessions. This problem does not affect the protection level.
- Statistics include information on detected objects only. If an object could not be scanned, this information is not included in a statistics report.
- The application settings are not automatically transferred when updating from the beta1 and beta2 versions.
- The application does not detect activity in the shared folders of legitimate software that could be used to damage the user's data or adware activity.
- The application may not determine the exact IP address or name of the remote machine that initiates malicious activity in the shared folders. However, the session of the attacking machine is blocked for a period specified in the settings.
- The application controls file changes initiated through the loopback interface (when performed network access to the shared resource of the local file system from the same workstation where the shared resource is located) for requests through the SMB protocol only.
- The application does not control file changes initiated by processes running at the operating system kernel level.
- As part of the rollback procedure, files can be downloaded from a cloud storage to the folder specified in the cloud storage settings.
- In the interval after installing the application and before restarting the computer, there is a restriction on file rollback. Their number is limited to 10.
- The Malware Scan feature does not scan symbolic links, locked files and archives content.
- Kaspersky Anti-Ransomware Tool for Home does not detect the EICAR test file.
- Changes to the application files and registry keys may cause the application malfunction.
- The Malware Scan feature does not detect a threat if the file path exceeds 260 characters.
- If you change the location of the Downloads folder, Kaspersky Anti-Ransomware Tool for Home will not scan files from this folder. To resume scanning, you need to restart the application.
Upgrade protection
To upgrade the application:
- Open the main application window.
- Go to the Upgrade protection section.
A comparison table of upgrade options opens.
By clicking the button Buy now you will be redirected to the web page where you can purchase the premium version of Kaspersky Total Security.
By clicking the button Try now you will be redirected to the web page where you can download Kaspersky Total Security available for free for 30-day period.
Page top
Anti-ransomware
Anti-ransomware components protect computers against ransomware applications that can, for example, block access to a computer system until a sum of money is paid. The anti-ransomware components are:
- KSN (Kaspersky Security Network). The cloud-based knowledge base containing information about the reputation of applications and websites. Use of data from Kaspersky Security Network ensures faster responses to threats, improves the performance of some protection components, and reduces the likelihood of false positives. To detect malicious objects based on KSN data, Kaspersky Anti-Ransomware Tool for Home analyzes both objects stored on the computer and HTTP traffic in order to evaluate the reputation of URLs associated with uploaded files.
- Behavior Detection. This component collects data on the actions of applications on your computer and provides this information to other protection components to improve their performance.
- Exploit Prevention. The component tracks executable files that are run by vulnerable applications. When there is an attempt to run an executable file from a vulnerable application that was not performed by the user, Kaspersky Anti-Ransomware Tool for Home blocks this file from running.
- Remediation Engine. The component rolls back actions that have been performed by malware in the operating system.
Anti-malware
These features are available in Premium. Increase your protection with Kaspersky Total Security.
- File Threat Protection. The File Threat Protection component lets you prevent infection of the file system of the computer. By default, the File Threat Protection component starts together with the app, continuously resides in the computer's RAM, and scans files that are opened or run on the computer and on its attached drives to find viruses and other potential threats.
- Web Threat Protection. The Web Threat Protection component protects incoming and outgoing data that is sent to and from the computer over the HTTP and FTP protocols and checks URLs against the list of malicious or phishing web addresses. The Web Threat Protection component intercepts every web page or file that is accessed by the user or an application via the HTTP or FTP protocol and analyzes them for viruses and other threats. If the page or file is found not to contain malicious code, the user gains immediate access to them.If a user accesses a web page or file that contains malicious code, the application performs the action that is specified in the Web Threat Protection component settings.
- Mail Threat Protection. The Mail Threat Protection component scans incoming and outgoing email messages for viruses and other threats. It starts together with the app, continuously remains active in computer memory, and scans all messages that are sent or received via the POP3, SMTP, IMAP, MAPI, and NNTP protocols. If no threats are detected in the email message, it becomes available and/or is processed.
- Network Threat Protection. The Network Threat Protection component scans inbound network traffic for activity that is typical of network attacks. Upon detecting an attempted network attack that targets your computer, the app blocks network activity from the attacking computer.
- AMSI Protection Provider is intended to support Antimalware Scan Interface from Microsoft. Antimalware Scan Interface (AMSI) allows a third-party application with AMSI support to send objects (for example, PowerShell scripts) to Kaspersky Endpoint Security for additional scan and to receive scan results for these objects. For details on AMSI refer to Microsoft documentation.
Data Encryption
These features are available in Premium. Increase your protection with Kaspersky Total Security.
These components let you encrypt files and folders that are stored on local and removable drives, or entire removable drives and hard drives. Data encryption minimizes the risk of information leaks that may occur when a portable computer, removable drive or hard drive is lost or stolen, or when data is accessed by unauthorized users or applications.
- Full Disk Encryption. Full disk encryption is a means of protecting information by encrypting all of the data on a disk, including temporary files, programs, and system files. If an attacker gains physical access to the device it’s protecting, such as in the event of theft, FDE will keep that data safe.
- Encryption of Removable Drives. The component protects all of the data on a removable drive.
Security Сontrols
These features are available in Premium. Increase your protection with Kaspersky Total Security.
- Application Control. The Application Control component monitors user attempts to start applications and regulates the startup of applications by using Application Control rules. When a user attempts to start an application that is blocked by Application Control rules, the component blocks this application from starting.
- Device Control. Device Control ensures the security of confidential data by restricting user access to devices that are installed on the computer or connected to it, including: data storage devices (hard drives, removable drives, tape drives, CD/DVD drives), data transfer tools (modems, external network cards), devices that are designed for converting data to hard copies (printers), connection buses, referring to interfaces for connecting devices to computers (such as USB, FireWire, and Infrared).
- Web Control. Web Control allows controlling actions by LAN users, by restricting or blocking access to web resources. Web Control provides the following options: saving traffic, delimiting access by content categories of web resources, centralized control of access to web resources.
- Adaptive Anomaly Control. The component is a smart tool for automated attack surface reduction. This technology enables you to customize system's hardening right down to the level of the individuals or different groups of users reflecting their various unique requirements while preventing the exploitation of the system's vulnerabilities or excessive functionality.
Install and uninstall the application
This section contains step-by-step instructions for Kaspersky Anti-Ransomware Tool for Home installation and removal.
Install the application
Kaspersky Anti-Ransomware Tool for Home is installed using the Setup Wizard that guides you through the steps of the setup process. The Back and Next buttons can be used to navigate between the screens of the Setup Wizard. The Cancel button allows you to exit the Setup Wizard.
To install Kaspersky Anti-Ransomware Tool for Home:
- Open the Kaspersky Anti-Ransomware Tool for Home setup file.
The Kaspersky Anti-Ransomware Tool for Home Setup Wizard opens.
- In the window that opens, carefully read End User License Agreement, Statement Regarding Data Processing For Marketing Purposes, Supplemental Statement On Data Processing, Privacy Policy, and do one of the following:
- If you agree to the terms and conditions, confirm that by selecting the appropriate check boxes.
- If you do not agree to the terms and conditions, cancel the installation of Kaspersky Anti-Ransomware Tool for Home and do not use the application.
- Select types of objects to be detected and blocked by the application.
- Wait for the installation of Kaspersky Anti-Ransomware Tool for Home to complete.
- If you do not want Kaspersky Anti-Ransomware Tool for Home to start automatically after you close the Setup Wizard, clear the Run Kaspersky Anti-Ransomware Tool for Home check box.
- Click Finish to quit the Setup Wizard.
Kaspersky Anti-Ransomware Tool for Home is now successfully installed on your computer.
Update the application
During the update, the Setup Wizard uninstalls the previous version of Kaspersky Anti-Ransomware Tool for Home and copies your application settings automatically.
Please make sure that the application folder has not been moved from the default installation path and is not read-only so that the Setup Wizard is able to copy your settings.
To update Kaspersky Anti-Ransomware Tool for Home:
- Download the latest version of the application.
- Open the Kaspersky Anti-Ransomware Tool for Home setup file.
The Kaspersky Anti-Ransomware Tool for Home Setup Wizard opens.
- In the window that opens, carefully read End User License Agreement, Statement Regarding Data Processing For Marketing Purposes, Supplemental Statement On Data Processing, Privacy Policy, and do one of the following:
- If you agree to the terms and conditions, confirm that by selecting the appropriate check boxes.
- If you do not agree to the terms and conditions, cancel the installation of Kaspersky Anti-Ransomware Tool for Home and do not use the application.
- Wait for the installation of Kaspersky Anti-Ransomware Tool for Home to complete.
The application prompts you to restart the computer.
- Click Restart now to finish the update.
After you restart the computer, Kaspersky Anti-Ransomware Tool for Home is updated.
Uninstall the application
You can uninstall the application using the Setup Wizard.
To uninstall Kaspersky Anti-Ransomware Tool for Home from a computer:
- Open the Control Panel in one of the following ways:
- If you use Windows 7, select Control Panel in the Start menu.
- If you use Windows 8 / Windows 8.1, press the Win + I shortcut and select the Control Panel item.
- If you use Windows 10, open the Start menu and start typing "control". Select the Control Panel item in the search results.
- In the window that opens, select Programs and Features.
- In the list of applications, select Kaspersky Anti-Ransomware Tool for Home and click Uninstall/Change.
The Setup Wizard opens.
- Click Next.
- Enter the password, if required.
Uninstallation of Kaspersky Anti-Ransomware Tool for Home starts.
- Wait for the uninstallation of Kaspersky Anti-Ransomware Tool for Home to complete.
- Restart your computer.
In some cases, the C:\Users\All Users\Kaspersky Lab\AntiRansom4 folder may remain after the application is uninstalled.
Data provision under the Supplemental Agreement
View the Statement on Data Processing
By accepting the terms of the Statement on Data Processing, you agree to automatically submit the information to Kaspersky via the installed application. The following data is processed:
- battery level and battery discharge rate;
- event date and time;
- additional information about OS features;
- information on network bandwidth and its usage;
- number of processor cores;
- logical processors count;
- current and maximum processor frequency;
- CPU usage information;
- information on disk usage (IOPS);
- disk operations count;
- device ID;
- information about system memory usage by the Software;
- operating system family;
- OS version, OS build number, OS update number, OS edition, extended information about the OS edition;
- OS Service Pack version;
- type of hardware platform;
- physical RAM size;
- data about a third-party application that had caused an error: the application image file name and path, the application image file size and checksum (MD5, SHA256, SHA-1), the application process identifier (PID), date and time of the application process image file compiling and creation, application process memory stack and application process memory address where an error had occurred, application uptime before the error had occurred, names, versions and checksums (MD5, SHA256, SHA-1) of the application components' files;
- Software language ID;
- date and time of creating an executable file being processed;
- application image size;
- checksum (MD5) of the object being processed;
- name of the object being processed;
- Software name;
- version of the object being processed;
- path to the object being processed;
- directory code;
- process system ID (PID);
- version of the Software's component;
- full version of the Software;
- Software update ID;
- Software ID;
- Software localization;
- Software rebranding ID;
- type of installed Software;
- the memory stack of the Software process failure;
- flag indicating whether the user has accepted the terms of the legal agreement while using the Software;
- type of legal agreement accepted by the user while using the Software;
- date and time when the user accepted the Agreement terms while using the Software;
- version of the legal agreement accepted by the user while using the Software;
- type of the hard drive;
- calculated size of the hard drive;
- name of the module in which the failure probably occurred;
- name of the process that caused software failure;
- duration of software operation until the failure;
- Software ID;
- Software installation/uninstallation status;
- installation error code;
- device type (laptop, desktop, tablet);
- OS type (server, workstation, domain controller);
- ID of the Software rebranding;
- installation type (new installation, update);
- ID of the marketing campaign;
- volume of inbound traffic;
- volume of outbound traffic;
- statistics message type;
- duration of third-party software operation until the failure;
- memory address with an offset, in which the third-party software failure occurred;
- information about failure in third-party software;
- name from the system log for the error occurred in third-party software.
- TFU ID of a company;
- step ID of the update process;
- step of the update process;
- number of update attempts;
- update error code;
- error message containing additional information about the current state of the application;
- start time of the fist update attempt;
- duration of the last update attempt;
- targeting status;
- registration form type;
- message indicating whether the operation was completed successfully;
- flag indicating whether the registration is complete;
- display frequency of the registration form;
- result of the event;
- flag indicating whether the internet connection is active;
- scan startup type;
- date and time of starting the scan operation;
- duration of the scan session;
- number of detected applications;
- number of vulnerable applications;
- number of new vulnerable applications since the previous scan;
- number of deleted vulnerable applications since the previous scan;
- number of updated applications that previously had vulnerabilities;
- number of vulnerabilities;
- result of the scan operation;
- number of attempts to enter the activation code;
- incorrect activation code error;
- product activation status.
Application interface
This section describes the primary elements of the application interface.
Registration
When you run the application for the first time, you will be offered to complete registration.
New users are required to register to use the full functionality of the application.
Please take the following steps:
- If you are not registered, fill out fields with corresponding information, carefully read and confirm Privacy Policy if you are agree to receive promotional offers, and press Register. We'll send you an activation code to the email you have specified. After that, you will be prompted to enter the activation code. You can change the email or resend an activation code if needed.
After the registration is complete, the activation code will be available on the About page.
- If you want to postpone the registration process or cannot complete it, you will be able to get back to it at any time.
- If you are registered, skip the registration form by pressing the Already registered button, and enter your activation code in a corresponding field.
The number of PC using the same registration is limited to 5.
Page top
Main application window
The main application window displays protection status and information about enabled protection technologies.
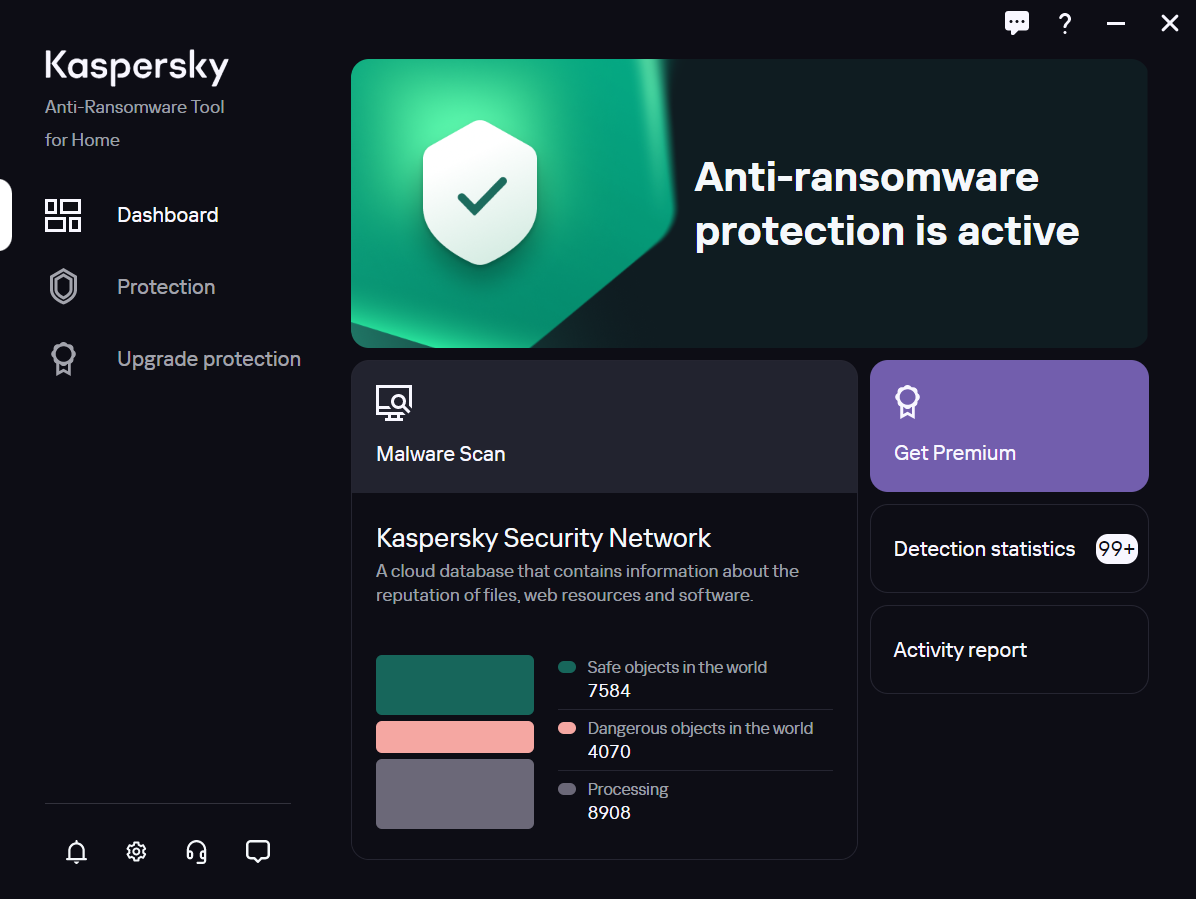
Main application window
The main application window contains a dashboard that lets you do the following:
- View the protection status
- See the statistics and go to Scan your PC for threats
- Get Premium
- See Detection statistics and go to the Detection statistics section for more details
- Go to the Activity report
In the main application menu you can switch between Dashboard, Protection and Upgrade protection sections.
The lower left corner of the main application window contains icons for going to unread news from Kaspersky  , Settings
, Settings ![]() , Get technical support section
, Get technical support section ![]() and feedback form
and feedback form ![]() .
.
In the upper right corner of each application window there is an icon for sending your feedback about the clarity of the window ![]() .
.
Application icon
The application icon ![]() appears in the taskbar notification area after installation of Kaspersky Anti-Ransomware Tool for Home.
appears in the taskbar notification area after installation of Kaspersky Anti-Ransomware Tool for Home.
In the context menu of the application icon, you can open the main application window, the application settings, or quit Kaspersky Anti-Ransomware Tool for Home.
Page top
Manage application notifications
Notifications that appear in the taskbar notification area inform you about application events that require your attention.
You can receive the following notifications:
- Detected objects—informs you that Kaspersky Anti-Ransomware Tool for Home has detected an object on the computer.
- Rolled back activity—informs you that Kaspersky Anti-Ransomware Tool for Home has detected an object on the computer and has successfully rolled back its actions.
- Machine blocked—informs you that Kaspersky Anti-Ransomware Tool for Home has detected a remote machine trying to encrypt a shared folder and has blocked its connection to the shared folder.
- Incorrect application settings—warns you that Kaspersky Anti-Ransomware Tool for Home could not perform tasks due to incorrect settings of the proxy server. These notifications may contain credentials fields or a link for opening the settings window.
- Prompts and action results—informs you about the results of checking the proxy server settings; prompts you to restart the computer, enter the password, or accept updated agreements.
- Log notifications—informs you that you have enabled logging of application events.
- News and special offers—informs you, for example, about Kaspersky sales or emerging cyberthreats.
- Feedback requests—lets you know that we would appreciate your feedback on the application.
- Safety status of uploaded files—informs you on the results of checking the files from the Downloads folder.
Some of the notifications contain the Get Premium link that directs you to the Kaspersky website where you can choose and purchase premium protection.
Notification balloons are not displayed while full-screen apps are running, except for the password and proxy data requests, and notifications about detected threats.
Page top
About window
The About window displays the version of the application and the activation code.
To open the About window:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- Switch to the About section.
Perform common tasks
This section contains step-by-step instructions for performing typical tasks that the Kaspersky Anti-Ransomware Tool for Home provides.
Onboarding
The first time you launch the application, you will be offered to take a tour of the product. The onboarding consists of the following steps:
- Protection status (describes where you can see if your device is currently under protection or not).
- Objects to detect (describes where and how you can choose which types of objects the application will detect).
- Detection statistic (shows where you can view the list of detected malicious objects).
- Email reporting (shows how you can send an email-report or manage its settings).
- Configure email reports.
- Malware Scan (highlights the area with the Malware Scan information).
- Activity report (highlights the area that guides you to a report on all the actions of the application).
- Help (on this screen you will learn how to go to Online help to find out more about the operation of the application).
After onboarding, you will be able to navigate in various areas of the application in order to use its main functions.
Page top
Configure and check the proxy server settings
If you use a proxy server to connect to the Internet, you must specify the proxy server connection settings.
By default, the application attempts to detect the proxy server settings and connect to the Internet automatically. If the application fails to detect the proxy server settings automatically, it prompts you to enter the user name and password for proxy server authentication. The application saves the specified user name and password automatically.
To configure the proxy server:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- In the Proxy settings section, select one of the following options:
- If you do not wish to use a proxy server to connect to the Internet, select Do not use proxy server.
- If you want the application to automatically configure the proxy server connection settings, select Detect proxy server settings automatically.
- To configure the proxy server connection settings manually, select Use specified proxy server settings and specify the address and port used to connect to the proxy server.
By default, port number 0 is used.
- If a user name and password must be specified when connecting to the proxy server, select the Use proxy server authentication check box and specify the user name and password to connect to the proxy server.
The password cannot be empty or contain quotation marks.
- If you want to use a proxy server only for outside resources, select the Bypass proxy server for local addresses check box.
Kaspersky doesn't receive any of this data. It is only used to generate and send reports to your system administrator.
To check the proxy server settings:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- In the Proxy settings section, click Check settings.
The application will establish a test connection with the Kaspersky servers. Results of the test will be displayed in a new window.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Page top
Enable notifications
To enable notifications on the safety status of downloaded files:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- Switch to the Notifications section.
- Check the Notifications on the safety of downloaded files check box.
The application will show notifications on the safety of .exe files in the Downloads folder.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Page top
Set the machine block time
If a remote machine tries to encrypt a shared folder, Kaspersky Anti-Ransomware Tool for Home will block the connection of the remote machine to the shared folder for the amount of time specified in the settings.
To set the machine block time:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- Switch to the Shared folders protection section.
- Specify the amount of minutes to block the connection. The maximum is 99 minutes.
- Save your changes.
The block time is set.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Page top
Types of objects to detect and block
To open the list of object types:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- Switch to the Types of objects section.
Here you can choose what type of objects to detect and block. There are two options:
- Malware is a software that fulfills the deliberately harmful intent of an attacker when run.
- Adware and others (including crypto-miners). Where adware is a class of programs that are designed to display advertisements on the user's computer, redirect your search requests to advertising websites and collect marketing-type data about the user – for example, the types of websites that the user visits – so that customized ads can be displayed. Other includes riskware, pornware and crypto-miners:
- Riskware legal programs that can cause damage to the computer if used by hackers to delete, block, modify or copy data.
- Pornware is a class of programs that find, download, and display pornographic material on a device.
- Crypto-miners is a class of programs that involves the unauthorized use of people's devices by cybercriminals to mine for cryptocurrency.
Check the required check boxes to enable corresponding types of objects.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Page top
Block exploits
Exploits take advantage of a bug or vulnerability to cause unintended behavior to occur on software. Kaspersky Anti-Ransomware Tool for Home tracks vulnerable applications for suspicious activity and blocks this activity. Information on the detection is stored to the reports.
System processes memory protection
Some software running on a user's computer have the ability to read system processes memory (for example, of the lsaas.exe process which can store user logins and passwords). You can additionally protect system processes memory from reading by external processes. For this feature, information on the detection is not stored to the reports or displayed in pop-up messages.
To turn on Exploit Prevention:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- In the Exploit Prevention section, flip on the Block exploits toggle switch.
- Flip on the Protect system processes memory toggle switch, if needed.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Page top
Password-protect the application settings
You can protect the settings with a password to prevent unauthorized or accidental modifications. When password-protected, exiting and uninstalling Kaspersky Anti-Ransomware Tool for Home (except via KavRemover) will also be restricted.
To password-protect the settings:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- In the Password section, flip on the Password-protect settings toggle switch.
- Enter and re-enter a password.
Your password cannot be empty or contain quotation marks.
- Click the Save button.
The application settings are protected with your password.
Unlock the application settings
Forgot your password? Reset the password
Page top
Exclusions
In this window you see two inserts: Trusted apps and Trusted machines. Switch between them to see lists of corresponding items added to Exclusions. If you add machine or application to the Exclusions, it means that you trust it and it will not be blocked by Kaspersky Anti-Ransomware Tool for Home even if it seems suspicious.
To add an application to the list of trusted applications:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- Switch to the Exclusions section.
- In the Trusted apps list, click Add apps and specify the path to an application file.
The application is added to the trusted list. Kaspersky Anti-Ransomware Tool for Home will not block this application.
You can unblock the applications that have been automatically blocked by Kaspersky Anti-Ransomware Tool for Home or move them to the list of trusted applications so that they will not be blocked in the future.
To remove an application from the list of trusted applications:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- Switch to the Exclusions section.
- In the Trusted apps list, select an application and click Remove.
The application is removed from the list of trusted applications.
To add a machine to the list of trusted machines:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
. - The Settings list opens.
- Switch to the Exclusions section.
- In the Trusted machines list, click Add machines and specify an IP-address.
- Click OK.
The machine is added to the trusted list. Kaspersky Anti-Ransomware Tool for Home will not block this machine.
To remove a machine from the list of trusted machines:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
. - The Settings list opens.
- Switch to the Exclusions section.
- In the Trusted machines list, select the machine and click Remove.
The machine is removed from the list of trusted machines.
For the Trusted machines feature to work, the Audit logon events function must be enabled in Windows settings.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Page top
Blocked items
If a remote machine or an application tries to encrypt a shared folder, Kaspersky Anti-Ransomware Tool for Home will block the connection of the remote machine to the shared folder or block the app. You can move the remote machines and apps that have been automatically blocked by Kaspersky Anti-Ransomware Tool for Home to the Exclusions so that they will not be blocked in the future. In the Blocked items window you see two inserts Blocked apps and Blocked machines with the lists if corresponding blocked items. From here you can unblock an item or move it to trusted.
To unblock an application:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
. - The Settings list opens.
- Switch to the Blocked items section.
- In the Blocked apps list, select the app and click Unblock.
The application is removed from the list of blocked applications. It may be blocked again in case of suspicious activity.
To move a blocked application to the list of trusted applications:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
. - The Settings list opens.
- Switch to the Blocked items section.
- In the Blocked apps list, select the app and click Move to trusted.
The application is removed from the blocked list and appears in the trusted list. Kaspersky Anti-Ransomware Tool for Home will not block this application.
To move a blocked machine to the list of trusted machines:
- Open the main application window.
- In the lower left corner of the main window, select Settings
 .
.The Settings list opens.
- Switch to the Blocked items section.
- In the Blocked machines list, select the machine and click Move to trusted.
The machine is moved to the trusted list. Kaspersky Anti-Ransomware Tool for Home will not block this machine.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Page top
View information on detected objects
To view information on detected objects:
- Open the main application window.
- On the dashboard click Detection statistics.
A list of detected objects opens.
- Click the
 icon next to a detected object to view detailed information about this object.
icon next to a detected object to view detailed information about this object. - If you need to clear the statistics on detected objects, click the Clear statistics button. Note that this option does not remove the detected ransomware from your PC or from the Ransomware Scan and Activity report.
The list on the Detection Statistics page may contain an unlimited number of objects.
Page top
Scan your PC for threats
Malware Scan
The Malware Scan feature allows to detect threats and block them. The Malware Scan runs automatically once a week. Customizing the scan schedule is only available in Premium, but you are free to run scanning anytime manually using Scan button and stop scanning using Cancel button.
After the scan is complete, you'll see the list of detected malware. This list contains up to 1000 of the most recent objects.
The feature doesn't remove threats, but only blocks them. However, you can remove detected threats manually. The paths to the detected files are specified in their description.
To open the Malware Scan window:
- Open the main application window.
- On the dashboard, click Scan PC for threats.
- Click the Malware Scan button.
The Malware Scan window opens.
Possible statuses:
- Scanned - the object was successfully scanned.
- Detected - the object is malicious.
- Not processed - the timeout for this object was exceeded, try to start Malware Scan once again.
Vulnerability Scan
This feature is in Beta version and may be unavailable for some users.
The Vulnerability Scan feature allows you to detect vulnerable applications installed on your PC. Such applications can be exploited by malware. The Vulnerability Scan runs automatically once a week. Customizing the scan schedule is only available in Premium, but you are free to run scanning anytime manually using Scan button and stop scanning using Cancel button.
After the scan is complete, you'll see the list of detected applications that have vulnerabilities and their versions. This list contains up to 1000 of the most recent objects.
To open the Vulnerability Scan window:
- Open the main application window.
- On the dashboard, click Scan PC for threats.
- Click the Vulnerability Scan button.
The Vulnerability Scan window opens.
Log application events
Diagnostic information about application events can be obtained using dump files, log files and ETL files. Technical Support may request these files to troubleshoot issues.
Dump files represent the state of the working memory of Kaspersky Anti-Ransomware Tool for Home at the moment these files are created. Dump files are generated automatically each time the application crashes. Dump files are stored in the folder %AllUsersProfile%\Kaspersky Lab\AntiRansom4\logs. These files have the AntiRansom*.dmp name format, where * stands for some additional details such as the application version or file creation date and time.
Log files are used to record detailed information about application activity. By default, logging of application events is disabled. Log files are stored in the folder %AllUsersProfile%\Kaspersky Lab\AntiRansom4\logs. These files have the AntiRansom*.log name format, where * stands for some additional details such as the application version or file creation date and time.
ETL files are generated automatically each time the application has a performance issue and are used to record information about the event. If it happens, you are prompted to send ETL files to Kaspersky for further analysis. ETL files are stored in the folder %AllUsersProfile%\Kaspersky Lab\AntiRansom4\logs. These files have the *.PERF*.etl name format, where * stands for some additional details such as the application version or file creation date and time.
Log files may take up a lot of disk space. It is recommended to enable logging on the request of Technical Support. After diagnostic information is collected, turn off logging to prevent running out of disk space.
To enable application logging:
- Open the main application window.
- In the lower left corner, click
 .
. - Scroll down and click Advanced.
- Select the Application logging check box.
When the check box selected, you can specify the detail level of logs.
- In the Detail level drop-down list, select one of the following levels:
- Recommended.
- Maximum.
Kaspersky Anti-Ransomware Tool for Home will log application events.
When you exit the Settings section, you will be prompted to save the changes or leave the section without saving. Don't forget to save the changes if you want them to apply.
Dump files and log files are stored in a non-encrypted format and may contain confidential data. You can view the contents of these files by opening one in a text editor (for example, Notepad). Dump files and log files are deleted permanently when the application is removed. Kaspersky does not automatically collect dump files or log files.
Page top
Activity report
The Activity report is a report that contains information about the actions performed by the application to protect the computer from threats. The report provides information on actions for the last 7 and 30 days. The report is automatically generated once a week, you will receive a notification as soon as it is generated. In addition, you can generate it manually at any time from the main application window.
To open the Activity report:
- Open the main application window.
- On the dashboard, click Activity report.
An Activity report window opens.
In the window you see a list of application actions and their statistics. By clicking the Details button, you will switch to the corresponding section of the application.
Page top
Manage the application from the Command Prompt
This section describes how to manage Kaspersky Anti-Ransomware Tool for Home at the command prompt.
Install the application in silent mode
You can install Kaspersky Anti-Ransomware Tool for Home in silent mode from the command prompt. Before installing the application, please open and carefully read the terms and conditions.
If you have Kaspersky Anti-Ransomware Tool for Home older than version 4.0 Patch M, you must uninstall the application manually and restart your computer before performing a silent installation. Otherwise, a system error may occur.
To install the application in silent mode:
- Please open and carefully read End User License Agreement, Statement Regarding Data Processing for Marketing Purposes, Supplemental Statement on Data Processing, Supplemental Statement on Data Processing and Privacy Policy.
- If you agree to the terms and conditions, continue to install the application.
- If you do not agree to the terms and conditions, do not install and do not use Kaspersky Anti-Ransomware Tool for Home.
- Start the command prompt.
- Enter
cd <path to the folder with the installation file> - Enter <
name_of_installation_file.exe> /q AGREETOEULA=1 AGREETO_SUPPLEMENTAL_STATEMENT=1 AGREETOPRIVACYPOLICY=1 AGREETO_MARKETING_STATEMENT=1 ADWARE_DETECT=1 <settings>[=<value>]Description of the parameters:
/q– enable silent mode.AGREETOEULA=1– use this parameter if you confirm that you have fully read, understand and accept the terms of the End User License Agreement. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.AGREETO_SUPPLEMENTAL_STATEMENT=1– use this parameter if you confirm that you have fully read, understand and accept the terms of the Supplemental Statement on Data Processing. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.AGREETOPRIVACYPOLICY=1– use this parameter if you confirm that you are aware and agree that your data will be handled and transmitted (including to third-party countries) as described in the Privacy Policy, and if you confirm that you have fully read and understand the Privacy Policy. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.AGREETO_MARKETING_STATEMENT=1– use this parameter if you confirm that you have fully read, understand and accept the terms of the Statement Regarding Data Processing for Marketing Purposes. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.ADWARE_DETECT=1– enable detection of adware and other legitimate software that could be used to harm your data. You can disable this function and detect only malware by enteringADWARE_DETECT=0. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.<settings>– specify additional settings.
All parameters are case-sensitive. Receiving the application error code
ErrorCode: 253alongside with an MSI error, indicates that the command did not use correct command syntax. Please review these instructions and try again. - Wait for the installation to finish.
After the installation is finished, the Kaspersky Anti-Ransomware Tool for Home icon appears on your desktop.
Update the application in silent mode
You can update Kaspersky Anti-Ransomware Tool for Home in silent mode from the command prompt. Before updating the application, please open and carefully read the terms and conditions.
To update the application in silent mode:
- Please open and carefully read End User License Agreement, Statement Regarding Data Processing For Marketing Purposes, Supplemental Statement On Data Processing, Supplemental Statement on Data Processing, and Privacy Policy, for using the application.
- If you agree to the terms and conditions, continue to update the application in silent mode.
- If you do not agree to the terms and conditions, do not update Kaspersky Anti-Ransomware Tool for Home.
- Start the command prompt.
- Enter
cd <path to the folder with the installation file> - Enter <
name_of_installation_file.exe> /q AGREETOEULA=1 AGREETO_SUPPLEMENTAL_STATEMENT=1 AGREETOPRIVACYPOLICY=1 AGREETO_MARKETING_STATEMENT=1 ADWARE_DETECT=1 REBOOTCOMPUTER=1 <settings>[=<value>]Description of the parameters:
/q– enable silent mode.AGREETOEULA=1– use this parameter if you confirm that you have fully read, understand and accept the terms of the End User License Agreement. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.AGREETO_SUPPLEMENTAL_STATEMENT=1– use this parameter if you confirm that you have fully read, understand and accept the terms of the Supplemental Statement on Data Processing. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.AGREETOPRIVACYPOLICY=1– use this parameter if you confirm that you are aware and agree that your data will be handled and transmitted (including to third-party countries) as described in the Privacy Policy, and if you confirm that you have fully read and understand the Privacy Policy. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.AGREETO_MARKETING_STATEMENT=1– use this parameter if you confirm that you have fully read, understand and accept the terms of the Statement Regarding Data Processing for Marketing Purposes. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.ADWARE_DETECT=1– enable detection of adware and other legitimate software that could be used to harm your data. You can disable this function and detect only malware by enteringADWARE_DETECT=0. If you don't enter this parameter, Kaspersky Anti-Ransomware Tool for Home won't be installed.REBOOTCOMPUTER=1 –restart the computer to finish updating. You can enterREBOOTCOMPUTER=0to restart manually.<settings> –specify additional settings.
All parameters are case-sensitive. Receiving the application error code
ErrorCode: 253alongside with an MSI error, indicates that the command did not use correct command syntax. Please review these instructions and try again. - Restart your computer.
The application is updated.
If you first need to export your application settings, run the anti_ransom_gui.exe file in the application folder with the exportsettings parameter. Your settings will be exported to c:\ProgramData\Kaspersky Lab\AntiRansom4\protected\settings_storage.xml.
When updating, the application edits the [HKEY_LOCAL_MACHINE\SOFTWARE\KasperskyLab\AntiRansom4] registry flag to "UpgradeFlag"=dword:00000001.
Uninstall the application in silent mode
You can uninstall Kaspersky Anti-Ransomware Tool for Home in silent mode from the command prompt.
To uninstall the application in silent mode:
- Start the command prompt.
- Enter
cd <path to the folder with the installation file> - Enter <
name_of_installation_file.exe> /q REMOVE=ALL - If you have previously set a password, you must provide it within the command with the PROTECTION_PASSWORD parameter.
- Your computer restarts automatically to completely uninstall the application. You can specify the additional REBOOTCOMPUTER parameter to avoid automatic restart. To do so, enter <
name_of_installation_file.exe> /q REMOVE=ALL REBOOTCOMPUTER=0All parameters are case-sensitive. Receiving the application error code
ErrorCode: 253alongside with an MSI error, indicates that the command did not use correct command syntax. Please review these instructions and try again.The application is uninstalled.
Application settings for the command prompt
When you install or update the application in silent mode, you can specify in your command the settings presented in the table below.
Use the following format: <settings>[=<value>]. For example, AGREETOEULA=1
If setting values contain spaces, enclose these values in double quotes. For example, PROXY_AUTH_LOGIN="My Login"
Application settings for the command prompt
Name |
Description |
Available values |
Required / optional |
AGREETOEULA |
Accept the terms and conditions of the End User License Agreement. |
0 – decline 1 – agree |
Always required |
AGREETO_SUPPLEMENTAL_STATEMENT |
Accept the terms and conditions of the Supplemental Statement on Data Processing. |
0 – decline 1 – agree |
Always required |
AGREETOPRIVACYPOLICY |
Accept the terms and conditions of the Privacy Policy. |
0 – decline 1 – agree |
Always required |
AGREETO_MARKETING_STATEMENT |
Accept the terms of the Statement Regarding Data Processing for Marketing Purposes. |
0 – decline 1 – agree |
Always required |
ADWARE_DETECT |
Turn on detection of adware and suspicious processes. |
0 – decline 1 – agree |
Always required |
PROXY_TYPE |
Type of proxy server use. If PROXY_TYPE = manually, the PROXY_HOST and PROXY_PORT parameters are required. |
auto – proxy server settings are detected automatically (by default) manually – configure the proxy server settings manually none – a proxy server is not used |
Optional |
PROXY_HOST |
Proxy server address. |
Arbitrary value |
Optional |
PROXY_PORT |
Port used to connect to the proxy server. |
[0-65535] |
Optional |
PROXY_AUTH_LOGIN |
User name to connect to the proxy server. |
Arbitrary value |
Optional |
PROXY_AUTH_PASSWORD |
Password to connect to the proxy server. The password cannot be empty or contain quotation marks. |
Arbitrary value |
Optional |
PROXY_LOCAL_ADDRESS |
Whether a proxy server is used for local addresses. |
0 – a proxy server is used 1 – a proxy server is not used (by default) |
Optional |
MIGRATE_SETTINGS |
Enable / disable settings migration from the previous version of the application. If enabled (or not specified) when updating the application in silent mode, only the always-required parameter values (AGREETOEULA, AGREETO_SUPPLEMENTAL_STATEMENT, AGREETOPRIVACYPOLICY, ADWARE_DETECT) will be used from a command. Optional and relative parameter values will be copied from the previously installed version. If the previously installed version is Beta1 or Beta2, the MIGRATE_SETTINGS value is ignored since automatic settings copying is not available for those versions. |
0 – disable 1 – enable (by default) |
Optional |
REBOOTCOMPUTER |
Restart the computer after uninstalling or updating the application. |
0 – do not restart 1 – restart |
Required if updating |
PROTECTION_PASSWORD |
Password-protect the application settings. Your password cannot be empty or contain quotation marks. |
Arbitrary string value |
Optional (incompatible with the PROTECTION_PASSWORD_PATH parameter) |
PROTECTION_PASSWORD_PATH |
Specify a local or network path to a TXT file with the password to protect the application settings. |
Arbitrary string value |
Optional (incompatible with the PROTECTION_PASSWORD parameter) |
REGISTRATION_CODE |
Code to activate the application. |
Arbitrary value |
Optional |
The following table describes specific settings intended for internal use at Kaspersky. We cannot guarantee correct installation and operation of the application if you modify the default values of these settings.
Application settings for internal use
Name |
Description |
Default value |
INSTALLDIR |
Internal setting for changing the default installation path of the application. |
The default installation path is C:\Program Files (x86)\Kaspersky Lab\Kaspersky Anti-Ransomware Tool for Home 4.0 for a 64-bit operating system. |
SELFPROTECTION |
Enable (1) / disable (0) self-protection. |
Self-protection is enabled by default. |
RUNAPP |
Run (1) / do not run (0) the application after installing in silent mode. |
The application is launched by default. |
/log <path to folder> |
Create application installer and MSI installer log files in the specified folder. The following file names will be used: "kart_installer_%m.%d_%H.%M.INST.log"; "kart_installer_%m.%d_%H.%M.MSI.log"; m – month, d – day, H – hour, M - minute. |
Not set |
/disable_updates |
Skip the search for installer updates, in case of launching without specifying the /q key |
Not set |
/wait |
Wait for the shut down of the already running installer before starting work |
Not set |
All parameters are case-sensitive. Receiving the application error code ErrorCode: 253 alongside with an MSI error, indicates that the command did not use correct command syntax. Please review these instructions and try again.
If you do not specify the optional parameters, Kaspersky Anti-Ransomware Tool for Home will be installed with the default values of these parameters.
Page top
Open Help on the command prompt
If you do not use correct command syntax when working with the application in the command prompt, for example, you have not specified the required parameters, the application will return the error code ErrorCode: 253 alongside with an MSI error and the link to this Help.
To open Help from the command prompt:
- Start the command prompt.
- Enter
cd <path to the folder with the installation file> - Enter <
name_of_installation_file.exe> /qThe link to this Help is shown.
Appendix 1. Network settings for interaction with external services
Kaspersky Anti-Ransomware Tool for Home uses the following network settings for interacting with external services:
Address |
Protocol |
Port |
Description |
|---|---|---|---|
|
HTTPS |
443 |
Updating databases and application modules. |
|
HTTPS |
443 |
Updating databases and application modules. Checking if Kaspersky servers are accessible. If access to the servers using system DNS is not possible, the application uses public DNS. This is necessary to make sure anti-virus databases are updated and the level of security is maintained for the computer. Kaspersky Anti-Ransomware Tool uses the following list of public DNS servers in the following order:
Requests emitted by the application may contain addresses of domains and the public IP address of the user because the application establishes a TCP/UDP connection with the DNS server. This information is needed, for example, to validate the certificate of a web resource when using HTTPS. If Kaspersky Anti-Ransomware Tool is using a public DNS server, data processing is governed by the privacy policy of the relevant service. |
|
HTTP |
80 |
Receiving the trusted time for checking the validity period of the certificate (TLS connection). |
|
HTTP |
80 |
Updating databases and application modules. |
|
HTTPS |
443 |
Using Kaspersky Security Network. |
|
Any |
443 1443 |
Using Kaspersky Security Network. |
|
HTTPS |
443 |
Follow links from the interface. |
|
HTTP |
80 |
Public Key Infrastructure (PKI) |
|
HTTPS |
443 |
User registration |
|
HTTPS |
443 |
Sending statistics |
|
HTTPS |
443 |
Downloading IPM content and sending IPM statistics. |
|
HTTPS |
443 |
Sending the application dump files and ETL logs. |
|
HTTPS |
443 |
Downloading new product versions. |
Get technical support
If you are having an issue with Kaspersky Anti-Ransomware Tool for Home, you can choose from different support options that are provided by Kaspersky:
- Technical Support
- Community
- Online Help
To open the list of support options:
- Open the main application window.
- In the lower left corner of the main application window, select
 .
.This opens a window showing the support options.
Support for this program is carried out in accordance with its life cycle, available on https://support.kaspersky.com/corporate/lifecycle.
Page top
Leave feedback
Tell us what you think about Kaspersky Anti-Ransomware Tool for Home or just rate the application. We might not have an opportunity to respond to you or solve your problem right away, but we appreciate any feedback and strive to make our products better.
To leave your feedback,
Click the Leave feedback icon ![]() in the lower left corner of the main application window and fill out the feedback form.
in the lower left corner of the main application window and fill out the feedback form.
Thank you!
Page top
Information about third-party code
Information about third-party code is contained in the file legal_notices.txt, in the application installation folder.
Page top
Trademark notices
Registered trademarks and service marks are the property of their respective owners.
Atom, Celeron, Intel and Pentium are trademarks of Intel Corporation or its subsidiaries.
Internet Explorer, Microsoft, Windows and Windows Server are trademarks of the Microsoft group of companies.
JavaScript is a registered trademark of Oracle and/or its affiliates.
Page top
Terms & Conditions
Statement Regarding Data Processing For Marketing Purposes
Supplemental Statement on Data Processing
Kaspersky Anti-Ransomware Tool for Home End User License Agreement
Supplemental Statement on Data Processing
Page top
STATEMENT REGARDING DATA PROCESSING FOR MARKETING PURPOSES (“MARKETING STATEMENT”)
Statement Regarding Data Processing For Marketing Purposes (hereinafter "Statement") relates to Kaspersky Anti-Ransomware Tool for Home (hereinafter "Software").
All terms used in this Statement have the same meaning defined in the End User License Agreement (EULA) under the paragraph "Definitions".
Please carefully read the terms of this Statement, as well as all documents referred to in this Statement, before accepting it. If the Software is used within a legal entity or on the Computer used by several individuals, You must ensure that they have understood and accepted the conditions of this Statement before data processing begins.
Data Protection and Processing
The Rightholder handles the data it receives from the End User under this Statement in accordance with the Rightholder’s Privacy Policy published at: https://www.kaspersky.com/Products-and-Services-Privacy-Policy.
Purposes of Data Processing
The Rightholder processes data for marketing purposes in accordance with this Statement in order:
- To improve the quality, appearance, and performance of the Rightholder’s Software, products, services, and infrastructure by analyzing users’ interactions, experience, and satisfaction;
- To offer You security solutions that best match Your needs;
- To provide You with the relevant content and advertisement;
- To create categories of groups of users based on certain parameters in order to provide relevant information to these groups about maintaining security level, marketing offers, and promotional materials.
Processed Data
Certain data which is processed under this Statement could be considered personal data according to laws of some countries. With Your consent, the following data will be automatically sent on a regular basis to the Rightholder under this Statement:
- OS bit size;
- device ID;
- operating system family;
- event type and value;
- version of the operating system;
- Software ID derived from the license;
- full version of the Software;
- Software update ID;
- Software localization;
- Software installation ID (PCID);
- Software rebranding ID;
- code of the partner organization associated with the Software rebranding;
- type of installed Software;
- user story name;
- Software ID;
- ID of the Software rebranding;
- version of the protocol of interaction between the Software and marketing messages;
- ID of the Software update start;
- web address being processed.
Your Choice to Participate
You can at any time withdraw Your consent by uninstalling the Software.
© 2023 AO Kaspersky Lab
Page top
SUPPLEMENTAL STATEMENT ON DATA PROCESSING (SUPPLEMENTAL STATEMENT)
Supplemental Statement On Data Processing (hereinafter “Statement”) relates to Kaspersky Anti-Ransomware Tool for Home (hereinafter “Software”).
All terms used in this Statement have the same meaning as defined in the “Definitions” clause of the End User License Agreement (EULA).
Please carefully read the terms of this Statement, as well as all documents referred to in this Statement, before accepting it. If the Software is used within a legal entity or on the Computer used by several individuals, You must ensure that they have understood and accepted the conditions of this Statement before data processing begins.
Data Protection and Processing
The Rightholder handles the data it receives from the End User under this Statement in accordance with the Rightholder’s Privacy Policy published at: https://www.kaspersky.com/products-and-services-privacy-policy.
Purposes of Processing Data
If a technical problem occurs during the use of the Software, You may send files with diagnostic information under this Statement to the Rightholder in order to improve the Software.
Preparing and Providing Files with Diagnostic Information
Files with diagnostic information are prepared in accordance with the User Manual. The files with diagnostic information are not sent to the Rightholder without Your consent. While the files with diagnostic information are stored on Your Computer, You are responsible for monitoring and limiting access to them until You transmit them to the Rightholder. By accepting this Statement, You confirm the absence of confidential data in the files with diagnostic information.
You may open the files with diagnostic information and view their contents before You make the decision to send them to the Rightholder.
With Your consent, the files with diagnostic information will be transmitted to the Rightholder, after which they will be deleted from your Computer. The transmission is performed using a secure channel.
Processed Data
Certain data which is processed under this Statement could be considered personal data according to laws of some countries. With Your consent, the following data will be sent to the Rightholder under this Statement:
- Memory dump files.
Include the memory contents of application (software) processes at the moment the dump is created; information necessary for software operation: settings, reports, internal databases, configuration files, and other data. They also contain data from trace files.
- Trace files.
- Information about the application: application ID; application version; application localization code; application name and type; application type ID; information about application customization; ID of the version of application settings.
- Information about the computer: unique ID of the computer; ID of the computer type.
- Information about the operating system (OS): OS name; OS version; OS type; OS bit type; the names and versions of installed updates.
- Information about the application installation: unique ID of the application installation on the computer; application installation type (first installation, upgrade); indicator of successful completion of installation or installation error number; indicator of user interruption of application installation.
- Information about apps started on the computer: hash (MD5) of the executable file and the number of file starts since the last time such information was submitted; full path to the executable file on the computer; identifier indicating whether or not the file has a valid digital signature; identifier indicating one of the standard paths to the location of the executable file in the system.
- Information about the scanned object: hash (MD5); category assigned to the scanned object; ID of the categorization source; information about the object vendor (vendor name); version of the scanned object.
- Information about the version of the file categorization databases used by the application; ID of the database record used during the scan; ID of the application component that requested the object category.
- Information about the scanned URL: URL; IP address of the categorized host to which the URL is assigned (name of the categories to which the URL is assigned; version and ID of the component that requested the categorization; ID of the reason for the request).
- Description of devices connected to the computer.
- Information about operation of the Rightholder's software updater component being used: version of the update component; error code of task termination if an error occurred; ID of the update task type; ID of the application status after the update; number of uncompleted update tasks during the entire operating time of the component; number of component health scan errors; name of the user who started the update task; information about names of the Rightholder's software files being updated, local paths to those files; data for proxy server authorization (logins, passwords).
- Information about the application status; information about user actions on the computer (start/stop of windows sessions, startup of apps) and application verdicts on actions; history of user actions and application activity.
- Information about started applications and their modules: file size; attributes; creation date; information about the process that loaded the file; information from the header; region; name; location; packers.
- Information about errors and use of the user interface of the installed Kaspersky Lab application.
- Information about network connections: the IP address of the remote computer and the user's computer; numbers of ports used to establish the connection; network protocol of the connection; information about network packets received by the computer and transmitted by the computer over a telecommunication network.
- Information about visited URLs (data on the user name and password used to access websites); contents of cookies; information about search queries.
- Original names of files.
- Names of categories of applications and websites.
- Date and time of events occurring in the operation of applications.
- Public certificate of the server.
- Other files.
In addition to the information above, in order to increase the processing speed of the request associated with the technical problems, You may specify the description of the problem occurred.
© 2021 AO Kaspersky Lab
Page top
KASPERSKY END USER LICENSE AGREEMENT (“LICENSE AGREEMENT”)
IMPORTANT LEGAL NOTICE TO ALL USERS: CAREFULLY READ THE FOLLOWING LEGAL AGREEMENT BEFORE YOU START USING THE SOFTWARE.
Running the Software, clicking the button that confirms that You accept the License Agreement during installation, or entering the corresponding character(s), constitutes Your unconditional acceptance of the terms of this License Agreement. If You do not agree with the terms of this License Agreement, You must abort the installation of the Software and\or delete the Software.
AFTER CLICKING THE BUTTON, THAT CONFIRMS YOUR ACCEPTANCE IN THE LICENSE AGREEMENT WINDOW OR AFTER ENTERING CORRESPONDING SYMBOL(S), YOU HAVE THE RIGHT TO USE THE SOFTWARE IN ACCORDANCE WITH THE TERMS AND CONDITIONS OF THIS AGREEMENT.
IF LICENSE CONTRACT OR SIMILAR DOCUMENT ACCOMPANIES SOFTWARE, TERMS OF THE SOFTWARE USE DEFINED IN SUCH DOCUMENT PREVAIL OVER THE CURRENT LICENSE AGREEMENT.
1. Definitions
1.1. Software means software including any Updates and related materials.
1.2. Rightholder (owner of all rights, whether exclusive or otherwise, to the Software) means AO Kaspersky Lab, a company incorporated according to the laws of the Russian Federation.
1.3. Computer(s) means combination of hardware(s), including personal computers, laptops, workstations, personal digital assistants, ‘smart phones’, hand-held devices, or other electronic devices, and operating system(s) (including system virtual machines) for which the Software was designed where the Software will be installed and/or used.
1.4. End User (You/Your) – means the organization for which the Software is downloaded or acquired and it is represented hereby that such organization has authorized the person accepting this agreement to do so on its behalf. For purposes hereof the term “organization,” without limitation, includes any partnership, limited liability company, corporation, association, joint stock company, trust, joint venture, labor organization, unincorporated organization, or governmental authority.
1.5. Update(s) means all upgrades, revisions, patches, enhancements, fixes, modifications, copies, additions, or maintenance packs, etc.
1.6. User Manual means user manual, administrator guide, reference book and related explanatory or other materials.
The on-line version of the User Manual is available on the Rightholder website: https://help.kaspersky.com/ and may be updated when necessary.
2. Grant of license
2.1. The Rightholder hereby grants You a non-exclusive license to store, load, install, execute, and display ("to use") the free of charge Software that will substantially perform within the scope of functionality described in the User Manual.
2.2. You have the right to make a copy of the Software solely for back-up purposes and only to replace the legally owned copy if such copy is lost, destroyed or becomes unusable. This back-up copy cannot be used for other purposes and must be destroyed when you lose the right to use the Software or when Your license expires or is terminated for any other reason according to the legislation in force in the country of your principal residence or in the country where You are using the Software.
2.3. From the time of the Software installation You have the right to receive the following services for the period of Term:
- Updates of the Software via the Internet when and as the Rightholder publishes them on its website or through other online services. Any Updates that you may receive become part of the Software and the terms and conditions of this Agreement apply to them;
- Access to information and auxiliary resources of the Rightholder.
3. Term and termination
3.1. The Software can be used free of charge after the acceptance of this Agreement for the period specified at https://support.kaspersky.com/corporate/lifecycle.
3.2. Without prejudice to any other remedy in law or in equity that the Rightholder may have, in the event of any breach by You of any of the terms and conditions of this Agreement, the Rightholder shall at any time without notice to You be entitled to terminate this License.
3.3. You agree that in using the Software and in using any report or information derived as a result of using this Software, you will comply with all applicable international, national, state, regional and local laws and regulations, including, without limitation, privacy, copyright, export control and obscenity law.
4. Technical Support
4.1. No Technical Support is provided.
4.2. Product consulting is available at https://community.kaspersky.com/ according to the rules of the Community.
5. Receiving informational and advertising materials
5.1. You acknowledge, accept and agree to receive informational materials via the Software from the Rightholder and/or Partners to improve the protection level.
6. Limitations
6.1. You shall not emulate, clone, rent, lend, lease, sell, modify, decompile, or reverse engineer the Software or disassemble or create derivative works based on the Software or any portion thereof with the sole exception of a non-waivable right granted to You by applicable legislation, and you shall not otherwise reduce any part of the Software to human readable form or transfer the licensed Software, or any subset of the licensed Software, nor permit any third party to do so, except to the extent the foregoing restriction is expressly prohibited by applicable law. Neither Software’s binary code nor source code may be used or reverse engineered to re-create the program algorithm, which is proprietary. All rights not expressly granted herein are reserved by the Rightholder and/or its suppliers, as applicable. Any such unauthorized use of the Software shall result in immediate and automatic termination of this Agreement and the License granted hereunder and may result in criminal and/or civil prosecution against You.
6.2. You shall not transfer the rights to use the Software to any third party.
6.3. You shall not rent, lease or lend the Software to any third party.
6.4. You shall not use the Software in the creation of data or software used for detection, blocking or treating threats described in the User Manual.
6.5. Violation of the intellectual rights to the Software shall result in civil, administrative or criminal liability in accordance with the law.
7. Limited Warranty and Disclaimer
7.1. The Software is intended to operate as described in the User Manual and, if supported versions of the Software are used, the installation by the End User of all the latest updates for the Software, unless otherwise stipulated in the License Agreement. The list of supported versions is available at https://support.kaspersky.com.
7.2. You acknowledge, accept and agree that no software is error-free and You are advised to back up the Computer with the frequency and reliability suitable for You.
7.3. The Rightholder does not provide any guarantee that the Software will work correctly in case of violations of the terms described in the User Manual or in this Agreement.
7.4. The Rightholder does not guarantee that the Software will work correctly if You do not regularly download Updates specified in Clause 2.3 of this Agreement.
7.5. You acknowledge that the Software will be provisioned with Rightholder's standard settings applied by default and that it is Your sole responsibility to configure the Software to satisfy Your own requirements.
7.6. THE SOFTWARE IS PROVIDED "AS IS" AND THE RIGHTHOLDER MAKES NO REPRESENTATION AND GIVES NO WARRANTY AS TO ITS USE OR PERFORMANCE. EXCEPT FOR ANY WARRANTY, CONDITION, REPRESENTATION OR TERM THE EXTENT TO WHICH CANNOT BE EXCLUDED OR LIMITED BY APPLICABLE LAW. THE RIGHTHOLDER AND ITS PARTNERS MAKE NO WARRANTY, CONDITION, REPRESENTATION, OR TERM (EXPRESSED OR IMPLIED, WHETHER BY STATUTE, COMMON LAW, CUSTOM, USAGE OR OTHERWISE) AS TO ANY MATTER INCLUDING, WITHOUT LIMITATION, NON-INFRINGEMENT OF THIRD-PARTY RIGHTS, MERCHANTABILITY, SATISFACTORY QUALITY, INTEGRATION, OR APPLICABILITY FOR A PARTICULAR PURPOSE. YOU ASSUME ALL FAULTS, AND THE ENTIRE RISK AS TO PERFORMANCE AND RESPONSIBILITY FOR SELECTING THE SOFTWARE TO ACHIEVE YOUR INTENDED RESULTS, AND FOR THE INSTALLATION OF, USE OF, AND RESULTS OBTAINED FROM THE SOFTWARE. WITHOUT LIMITING THE FOREGOING PROVISIONS, THE RIGHTHOLDER MAKES NO REPRESENTATION AND GIVES NO WARRANTY THAT THE SOFTWARE WILL BE ERROR-FREE OR FREE FROM INTERRUPTIONS OR OTHER FAILURES OR THAT THE SOFTWARE WILL MEET ANY OR ALL OF YOUR REQUIREMENTS WHETHER OR NOT DISCLOSED TO THE RIGHTHOLDER.
8. Exclusion and Limitation of Liability
8.1. TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, IN NO EVENT SHALL THE RIGHTHOLDER OR ITS PARTNERS BE LIABLE FOR ANY SPECIAL, INCIDENTAL, PUNITIVE, INDIRECT, OR CONSEQUENTIAL DAMAGES WHATSOEVER (INCLUDING, BUT NOT LIMITED TO, DAMAGES FOR LOSS OF PROFITS OR CONFIDENTIAL OR OTHER INFORMATION, FOR BUSINESS INTERRUPTION, FOR LOSS OF PRIVACY, FOR CORRUPTION, DAMAGE AND LOSS OF DATA OR PROGRAMS, FOR FAILURE TO MEET ANY DUTY INCLUDING ANY STATUTORY DUTY, DUTY OF GOOD FAITH OR DUTY OF REASONABLE CARE, FOR NEGLIGENCE, FOR ECONOMIC LOSS, AND FOR ANY OTHER PECUNIARY OR OTHER LOSS WHATSOEVER) ARISING OUT OF OR IN ANY WAY RELATED TO THE USE OF OR INABILITY TO USE THE SOFTWARE, THE PROVISION OF OR FAILURE TO PROVIDE SUPPORT OR OTHER SERVICES, INFORMATION, SOFTWARE, AND RELATED CONTENT THROUGH THE SOFTWARE OR OTHERWISE ARISING OUT OF THE USE OF THE SOFTWARE, OR OTHERWISE UNDER OR IN CONNECTION WITH ANY PROVISION OF THIS AGREEMENT, OR ARISING OUT OF ANY BREACH OF CONTRACT OR ANY TORT (INCLUDING NEGLIGENCE, MISREPRESENTATION, ANY STRICT LIABILITY OBLIGATION OR DUTY), OR ANY BREACH OF STATUTORY DUTY, OR ANY BREACH OF WARRANTY OF THE RIGHTHOLDER OR ANY OF ITS PARTNERS, EVEN IF THE RIGHTHOLDER OR ANY PARTNER HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES.
YOU AGREE THAT IN THE EVENT THE RIGHTHOLDER AND/OR ITS PARTNERS ARE FOUND LIABLE, THE LIABILITY OF THE RIGHTHOLDER AND/OR ITS PARTNERS SHALL BE LIMITED BY THE COSTS OF THE SOFTWARE. IN NO CASE SHALL THE LIABILITY OF THE RIGHTHOLDER AND/OR ITS PARTNERS EXCEED THE FEES PAID FOR THE SOFTWARE TO THE RIGHTHOLDER OR THE PARTNER (AS MAY BE APPLICABLE).
NOTHING IN THIS AGREEMENT EXCLUDES OR LIMITS ANY CLAIM FOR DEATH AND PERSONAL INJURY. FURTHER IN THE EVENT ANY DISCLAIMER, EXCLUSION OR LIMITATION IN THIS AGREEMENT CANNOT BE EXCLUDED OR LIMITED ACCORDING TO APPLICABLE LAW THEN ONLY SUCH DISCLAIMER, EXCLUSION OR LIMITATION SHALL NOT APPLY TO YOU AND YOU CONTINUE TO BE BOUND BY ALL THE REMAINING DISCLAIMERS, EXCLUSIONS AND LIMITATIONS.
9. GNU and Other Third-Party Licenses
9.1. The Software may include some software programs that are licensed (or sublicensed) to the user under the GNU General Public License (GPL) or other similar free software licenses which, among other rights, permit the user to copy, modify and redistribute certain programs, or portions thereof, and have access to the source code "Open-Source Software"). If such licenses require that for any software, which is distributed to someone in an executable binary format, that the source code also be made available to those users, then the source code should be made available by sending the request to source@kaspersky.com or the source code is supplied with the Software. If any Open-Source Software licenses require that the Rightholder provide rights to use, copy or modify an Open-Source Software program that are broader than the rights granted in this Agreement, then such rights shall take precedence over the rights and restrictions herein.
10. Intellectual Property Ownership
10.1. You agree that the Software and the authorship, systems, ideas, methods of operation, documentation and other information contained in the Software are proprietary intellectual property and/or the valuable trade secrets of the Rightholder or its Partners and that the Rightholder and its Partners, as applicable, are protected by civil and criminal law, and by the law of copyright, trade secret, trademark and patents of the Russian Federation, European Union and the United States, as well as other countries and international treaties.
This License Agreement does not grant You any rights to the intellectual property, including any Trademarks or Service Marks of the Rightholder and/or its Partners ("Trademarks"). You may use the Trademarks only insofar as to identify printed output produced by the Software in accordance with accepted trademark practice, including identification of the Trademark owner’s name. Such use of any Trademark does not give you any rights of ownership in that Trademark.
The Rightholder and/or its Partners own and retain all right, title, and interest in and to the Software, including without limitation any error corrections, enhancements, Updates or other modifications to the Software, whether made by the Rightholder or any third party, and all copyrights, patents, trade secret rights, trademarks, and other intellectual property rights therein.
Your possession, installation or use of the Software does not transfer to you any title to the intellectual property in the Software, and you will not acquire any rights to the Software except as expressly set forth in this License Agreement. All copies of the Software made hereunder must contain the same proprietary notices that appear on and in the Software. Except as stated herein, this License Agreement does not grant you any intellectual property rights in the Software and you acknowledge that the license, as further defined herein, granted under this License Agreement only provides you with a right of limited use under the terms and conditions of this License Agreement. Rightholder reserves all rights not expressly granted to you in this License Agreement.
10.2. You agree not to modify or alter the Software in any way. You may not remove or alter any copyright notices or other proprietary notices on any copies of the Software.
10.3. Violation of the intellectual rights to the Software shall result in civil, administrative or criminal liability in accordance with the law.
11. Governing Law
11.1. Except as provided in Sections A Clauses 11.2 and 11.3 below, this License Agreement shall be governed by and construed in accordance the laws specified below for the country or territory in which You obtained the Software, without reference to or application of conflicts of laws principles:
a. Russia. If you obtained the Software in Russia, the laws of the Russian Federation.
b. United States, Puerto Rico, American Samoa, Guam, and U.S. Virgin Islands. If you obtained the Software in the United States, Puerto Rico, American Samoa, Guam or the U.S. Virgin Islands, the laws of the Commonwealth of Massachusetts, USA, provided, however, that the laws of the U.S. state where you live will govern claims under state consumer protection, unfair competition, or similar laws. To the fullest extent permitted by law, the Rightholder and you expressly agree hereby to waive any right to a trial by jury.
c. Canada. If you obtained the Software in Canada, the laws of the Province of Ontario.
d. Mexico. If you obtained the Software in Mexico, the federal laws of the Republic of Mexico.
e. European Union (EU). If you obtained the Software in a member country of the EU, the laws of Germany.
f. Australia. If you obtained the Software in Australia, the laws of the State or Territory in which you obtained the license.
g. Hong Kong Special Administrative Region (SAR) and Macau SAR. If you obtained the Software in Hong Kong SAR or Macau SAR, the laws of Hong Kong SAR.
h. Taiwan. If you obtained the Software in Taiwan, the laws of Taiwan.
i. Japan. If you obtained the Software in Japan, the laws of Japan.
j. Any Other Country or Territory. If you choose to obtain the Software in another country, the substantive laws of the country where the purchase took place will be in effect.
11.2. Notwithstanding the foregoing, if the mandatory laws or public policy of any country or territory in which this License Agreement is enforced or construed prohibit the application of the law specified herein, then the laws of such country or territory shall instead apply to the extent required by such mandatory laws or public policy. Similarly, if you are an individual consumer, the provisions of Section A Clause 11.1 shall not affect any mandatory right you may have to take action in your country of residence under the laws of that country.
11.3. This License Agreement shall not be governed by the United Nations Convention on Contracts for the International Sale of Goods, the application of which is expressly excluded.
11.4. The End User is responsible for contacting only the Rightholder or their Partners directly if having any problems with the product.
12. Period for Bringing Actions
12.1. No action, regardless of form, arising out of the transactions under this Agreement may be brought by either party hereto more than one (1) year after the cause of action has occurred, or was discovered to have occurred, except that an action for infringement of intellectual property rights may be brought within the maximum applicable statutory period.
13. Entire Agreement; Severability; No Waiver
13.1. This Agreement is the entire agreement between you and Rightholder and supersedes any other prior agreements, proposals, communications or advertising, oral or written, with respect to the Software or to the subject matter of this Agreement. You acknowledge that you have read this Agreement, understand it and agree to be bound by its terms. If any provision of this Agreement is found by a court of competent jurisdiction to be invalid, void, or unenforceable for any reason, in whole or in part, such provision will be more narrowly construed so that it becomes legal and enforceable, and the entire Agreement will not fail on account thereof and the balance of the Agreement will continue in full force and effect to the maximum extent permitted by law or equity while preserving, to the fullest extent possible, its original intent. No waiver of any provision or condition herein shall be valid unless in writing and signed by you and an authorized representative of Rightholder provided that no waiver of any breach of any provisions of this Agreement will constitute a waiver of any prior, concurrent or subsequent breach. Rightholder’s failure to insist upon or enforce strict performance of any provision of this Agreement or any right shall not be construed as a waiver of any such provision or right.
14. Class Action Waiver and Binding Arbitration
14.1. If you reside in the United States, this Clause 14 from Section A applies to you. If a dispute, claim, or controversy of any kind with respect to any Rightholder product, service, or any part of this License Agreement, arises between You and Rightholder or You and a third-party affiliate of Rightholder, and both parties couldn't resolve the dispute informally within a reasonable period of time, You and the other party agree to binding individual arbitration before the American Arbitration Association ("AAA") under the Federal Arbitration Act ("FAA"), and not to sue in court in front of a judge or jury. In the event of a binding individual arbitration proceeding between parties, a neutral arbitrator will decide and the arbitrator’s decision will be final except for a limited right of appeal under the FAA. If any conflict exists between this License Agreement and the rules of the AAA, this License Agreement shall govern.
14.2. Any proceedings, including but not limited to class action lawsuits, class-wide arbitrations, private attorney-general actions, the combining of individual actions without the consent of all parties, or any other legal procedure where someone acts in a representative capacity, are not permitted. By accepting this License Agreement, You agree not to begin or participate in any of the above mentioned class and multi-party proceedings, and any action pursued by You and remedy, if any awarded to You, must be on an individual basis, as provided in this clause. You may contact the Rightholder or their Partners directly if having any problems with the product.
14.3. Any dispute, claim, or controversy concerning Rightholder's intellectual property rights, their enforcement, validity, etc., and any claim pertaining to any form of unauthorized use, including but not limited to theft and piracy, of any Rightholder product or service are not subject to this arbitration clause.
15. Rightholder Contact Information
Should you have any questions concerning this Agreement, or if you desire to contact the Rightholder for any reason, please contact our Customer Service Department at:
AO Kaspersky Lab, 39A/3 Leningradskoe Shosse
Moscow, 125212 Russian Federation
E-mail: info@kaspersky.com
Web site: https://www.kaspersky.com/
© 2023 AO Kaspersky Lab
Page top
SUPPLEMENTAL STATEMENT ON DATA PROCESSING (SUPPLEMENTAL STATEMENT)
Supplemental Statement On Data Processing (hereinafter “Statement”) relates to Kaspersky Anti-Ransomware Tool for Home (hereinafter “Software”).
All terms used in this Statement have the same meaning as defined in the “Definitions” clause of the End User License Agreement (EULA).
This Statement along with the EULA for the Software, in particular in the Section “Conditions regarding Data Processing,” specifies the conditions, responsibilities, and procedures relating to transmission and processing of the data indicated in this Statement.
Please carefully read the terms of this Statement, as well as all documents referred to in this Statement, before accepting it. If the Software is used within a legal entity or on the Computer used by several individuals, You must ensure that they have understood and accepted the conditions of this Statement before data processing begins.
Data Protection and Processing
The Rightholder handles the data it receives from the End User under this Statement in accordance with the Rightholder’s Privacy Policy published at: https://www.kaspersky.com/products-and-services-privacy-policy.
Purpose of Data Processing
To make it possible to increase the Software’s speed of reaction to information and network security threats.
The purpose is achieved by:
- determining the reputation of scanned objects;
- identifying information security threats that are new and challenging to detect, and their sources;
- taking prompt measures to increase the protection of the data stored and processed by the End User on the Computer;
- reducing the likelihood of false positives;
- increasing the efficiency of Software components;
- investigating of infection of a user’s computer;
- improving the performance of the Rightholder’s products;
- receiving reference information about the number of objects with known reputation.
Processed Data
Certain data which is processed under this Statement could be considered personal data according to laws of some countries. During use of the Software, the Rightholder automatically receives and processes the following data:
- fragment content of the object being processed;
- date and time when the certificate expires;
- date and time when the certificate was issued;
- version of list of revoked Software service's decisions;
- event date and time;
- text of the error message;
- number of update-apply cycles for anti-virus databases;
- date and time when the anti-virus databases were last updated and applied;
- the Software database record version;
- ID of the triggered record in the Software's anti-virus databases;
- timestamp of the triggered record in the Software's anti-virus databases;
- type of the triggered record in the Software's anti-virus databases;
- release date and time of the Software's databases;
- OS bit size;
- additional information about OS features;
- full version of the OS kernel;
- additional information about CPU features;
- flag indicating that the user device is a virtual machine;
- device ID;
- OS build number;
- extended information about the OS edition;
- operating system family;
- OS version, OS build number, OS update number, OS edition, extended information about the OS edition;
- OS ID;
- OS Service Pack version;
- date and time of the OS launch;
- type of hardware platform;
- CRC32 checksum of the user account security identifier;
- Device Guard (windows) enablement status;
- version of the operating system;
- IP address;
- version of the operating system installed on the user's computer;
- ID of the key from the keystore used for encryption;
- user login for the Web-Portal account;
- version of KSN request about file reputation;
- the config identifier;
- protocol used to exchange data with KSN;
- ID of the KSN service accessed by the Software;
- encryption characteristics of data package that is being sent to KSN;
- ID of data package that is being sent to KSN;
- installation type of software update;
- fragment order in the object being processed;
- data of the internal log, generated by the anti-virus Software module for an object being processed;
- contents of the digital certificate being processed;
- certificate issuer name;
- public key of the certificate;
- calculation algorithm of public key of the certificate;
- certificate serial number;
- date and time of signing the object;
- certificate owner name and settings;
- digital certificate thumbprint of the scanned object and hashing algorithm;
- date and time of the last modification of the object being processed;
- date and time of creating an object being processed;
- detect characteristics;
- objects or its parts being processed;
- description of an object being processed as defined in the object properties;
- format of the object being processed;
- checksum type for the object being processed;
- checksum (MD5) of the object being processed;
- name of the object being processed;
- checksum (SHA256) of the object being processed;
- size of the object being processed;
- name of the detected malware or legitimate software that can be used to damage the user's device or data;
- Software vendor name;
- the Software's decision on the object being processed;
- version of the object being processed;
- source of the decision made for the object being processed;
- checksum of the object being processed;
- parent application name;
- result of the module integrity check;
- path to the object being processed;
- directory code;
- information about file signature check results;
- operating system bit version;
- OS edition;
- Software ID derived from the license;
- date and time of System Watcher start;
- version of the Software's component;
- full version of the Software;
- ID of the topic in the Software help;
- Software update ID;
- Software ID;
- installation date and time for the Software;
- Software localization;
- full name of the partner organization through which the Software license order was placed;
- Software installation ID (PCID);
- Software rebranding ID;
- full version of the Software before upgrade;
- number of detects by the Software;
- number of the objects, detected by the Software;
- code of the partner organization associated with the Software rebranding;
- the Software screens, events on the Software screens, duration of the Software screen displaying;
- Software health status after update;
- information about date and frequency of sending KSN statistics by the Software;
- information about the Software state when sending the KSN statistics;
- type of installed Software;
- flag indicating whether the Software is connected to Web-Portal;
- the Software update date and time;
- flag indicating whether participation in KSN is enabled;
- format of the data in the request to Rightholder infrastructure;
- Software group;
- link name;
- the Software component ID;
- logon session key;
- encryption algorithm for the logon session key;
- the result of the Software action;
- flag indicating whether the user has accepted the terms of the legal agreement while using the Software;
- type of legal agreement accepted by the user while using the Software;
- date and time when the user accepted the Agreement terms while using the Software;
- version of the legal agreement accepted by the user while using the Software;
- date and time when statistics stopped being received;
- error code;
- Software ID;
- Software installation/uninstallation status;
- installation error code;
- flag indicating whether the installation was aborted by the user;
- device type (laptop, desktop, tablet);
- OS type (server, workstation, domain controller);
- ID of the Software rebranding;
- duration of Software installation in seconds;
- installation type (new installation, update);
- version of the protocol of interaction between the Software and marketing messages;
- number of KSN connections taken from the cache;
- number of requests for which a response was found in the local request database;
- number of unsuccessful KSN connections;
- number of unsuccessful KSN transactions;
- temporal distribution of cancelled requests to KSN;
- temporal distribution of unsuccessful KSN connections;
- temporal distribution of unsuccessful KSN transactions;
- temporal distribution of successful KSN connections;
- temporal distribution of successful KSN transactions;
- temporal distribution of successful requests to KSN;
- temporal distribution of requests to KSN that timed out;
- number of new KSN connections;
- number of unsuccessful requests to KSN caused by routing errors;
- number of unsuccessful requests caused by KSN being disabled in the Software settings;
- number of unsuccessful requests to KSN caused by network problems;
- number of successful KSN connections;
- number of successful KSN transactions;
- total number of requests to KSN;
- code integrity options;
- hypervisor support mode;
- OS version supported by software drivers;
- OS version supported by software drivers;
- current operating mode of software drivers;
- information about problems with third-party software;
- date and time when statistics started being received;
- probability of sending statistics by System Watcher;
- code of the event that took longer than the standard time to process by System Watcher;
- database processing time of the event that took longer than the standard time to process by System Watcher;
- processing delay time of the event about OS action in the behavioral analysis subsystem;
- number of delayed OS action events of the current type;
- maximum allowed time for processing an event by System Watcher;
- processing delay time of the event about OS action in the proactive defense subsystem;
- number of processed OS action events;
- number of processed synchronous OS action events;
- total delay of all OS action events of the current type;
- processing delay time of the event about OS action in the persistent event storage subsystem;
- processing time of the event that took longer than the standard time to process by System Watcher;
- total number of events that took longer than the standard time to process by System Watcher;
- total delay of all OS action events;
- number of waiting synchronous OS action events;
- date and time of detecting software by System Watcher;
- number of the detected software in the System Watcher context;
- reason of detecting software by System Watcher;
- date and time of received event of an action in the OS;
- code of the event that caused an event queue overflow while being processed by System Watcher;
- number of events that caused an event queue overflow while being processed by System Watcher;
- total number of queue overflows for events being processed by System Watcher;
- time difference between the first event in the queue and the current event when sending statistics package by System Watcher;
- type of the event that was timed out while being processed (klif/swmon);
- major and minor numbers of the interception filter that caused the interception that was timed out while being processed in System Watcher;
- ID of the interception that was timed out while being processed in System Watcher;
- number of klif events that were timed out when sending statistics package by System Watcher;
- queue size of the System Watcher events that were timed out while being processed;
- number of System Monitor events that were timed out when sending statistics package by System Watcher;
- storage time for object being processed;
- algorithm for calculating the digital certificate thumbprint;
- number of failed update installations for the updater component;
- number of update installation error for the updater component;
- error code of software update installation;
- error code of the update task;
- ID of the Software update start;
- update task type;
- version of the updater component;
- description of user registration error;
- statuses of filling in the fields in user registration form;
- ID of user registration form;
- serial number of user registration offer;
- user registration type;
- user registration error code;
- ID of the user of the Rightholder's website;
- accessed address of the web service (URL, IP);
- port number;
- web address of the source of the web service request (referer);
- web address being processed;
- IP address of the update source;
- number of files downloaded during one session with the update source;
- total amount of downloaded information;
- average speed of network operations with the update source;
- type of server usage error;
- ID of the product installation;
- ID of the device;
- type of the product;
- product full version;
- domain name of the Kaspersky infrastructure that was resolved;
- IP address of the selected DNS server;
- port opening timeout;
- flag indicating whether the DNS server is blocked;
- response status of the DNS server;
- predefined type to which the error belongs;
- error code;
- extended error information;
- information about the application that failed to install system call hooks;
- full build number of the OS Kernel;
- flag indicating whether the product self-defense is on;
- parameter indicating whether the feature is turned on;
- flag indicating whether the variable is resolved;
- flag indicating whether the path exists;
- flag indicating whether the path represents a directory or a file;
- flag indicating whether there is a symlink in the path;
- flag indicating whether there is a network path;
- flag indicating whether there are Unicode characters in the path to the folder;
- language of the OS;
- length of the path;
- version of the statistics being sent;
- detect characteristics;
- Software verdict on the object being processed;
- ID of the triggered record in the Software's anti-virus databases;
- timestamp of the triggered record in the Software's anti-virus databases;
- type of the triggered Software anti-virus databases record;
- release date and time of the Software's databases;
- vulnerability ID;
- vulnerability danger class;
- object type code;
- flag indicating whether the object being processed is a PE file;
- ID of the task in which detection was performed;
- detect characteristics;
- timestamp of the root index of available updates;
- code of the error category;
- component name;
- timestamp of the root index of updates being downloaded;
- timestamp of the component (local version);
- timestamp of the update component (updated version);
- type of dump created by the Software;
- name of the original index file downloaded during the last update;
- date and time of downloading local original index file;
- image name of the process the dump of which was detected by the Software;
- name of the module in which the failure probably occurred;
- date and time of dump creation.
The Rightholder also processes data in a form that does not, on its own, permit direct association with any specific individual. You can find the list of such data and purposes of their processing for a given Software by visiting https://help.kaspersky.com, selecting the Software, and viewing its respective “Data provision” section.
Your Choice to Participate
It is entirely Your choice to automatically send data on a regular basis to the Rightholder under this Statement. You can at any time withdraw Your consent by uninstalling the Software.
Please keep in mind that data processing by the Rightholder is based on legal bases, such as legitimate interest according to point (f) of Article 6 (1) of the EU General Data Protection Regulation (GDPR) or contract, as well as your given consent. This is why when you decide to withdraw your consent by uninstalling the Software or your license agreement expires, certain data already received may still be processed under legitimate interest for the purposes described in the Privacy Policy at https://www.kaspersky.com/Products-and-Services-Privacy-Policy, except where such legitimate interest is overridden by the interests or fundamental rights and freedoms of the User. If You wish to object to such data processing, You must inform us in the manner specified in the Privacy Policy. When your license agreement expires or you withdraw your consent, the Rightholder will not receive new data from you.
© 2023 AO Kaspersky Lab
Page top