Adding rules for parsing events from Kaspersky CyberTrace in FortiSIEM
This section describes how to add rules in FortiSIEM for parsing events that arrive from Kaspersky CyberTrace.
To add rules in FortiSIEM for parsing events:
- Open the FortiSIEM web console.
- Select Admin > Device Support > Parser.
- Select the parser after which you want to add a new one and click New.
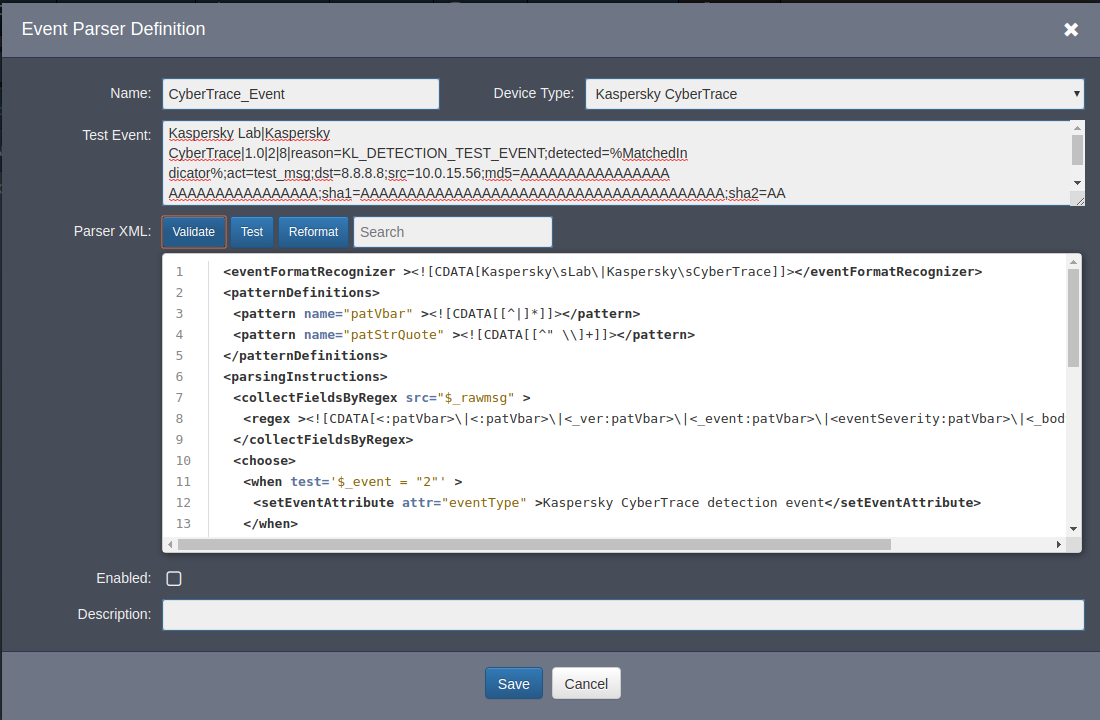
The Event Parser Definition window opens.
- Specify the following values:
- In the Name field, specify CyberTrace_Event.
- In the Device Type field, select Kaspersky CyberTrace.
- In the Test Event field, specify the following value:
Kaspersky Lab|Kaspersky CyberTrace|1.0|2|8|reason=KL_DETECTION_TEST_EVENT;detected=%MatchedIndicator%;act=test_msg;dst=8.8.8.8;src=10.0.15.56;md5=AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA;sha1=AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA;sha2=AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA;request=http://test.test;dvc=127.0.0.5;sourceServiceName=TEST_DEVICE;suser=test_user;msg=there_is_some_context:true and_more:true
Kaspersky Lab|Kaspersky CyberTrace|1.0|1|4|alert=KL_TEST_ALERT;msg=there_is_some_context:true and_more:true
- In the Parser XML field, specify the following value:
<eventFormatRecognizer>
<![CDATA[Kaspersky\sLab\|Kaspersky\sCyberTrace]]>
</eventFormatRecognizer>
<patternDefinitions>
<pattern name="patVbar" ><![CDATA[[^|]*]]></pattern>
<pattern name="patStrQuote" ><![CDATA[[^" \\]+]]></pattern>
</patternDefinitions>
<parsingInstructions>
<collectFieldsByRegex src="$_rawmsg" >
<regex>
<![CDATA[<:patVbar>\|<:patVbar>\|<_ver:patVbar>\|<_event:patVbar>\|<eventSeverity:patVbar>\|<_body:gPatMesgBody>]]>
</regex>
</collectFieldsByRegex>
<choose>
<when test='$_event = "2"' >
<setEventAttribute attr="eventType" >Kaspersky CyberTrace detection event</setEventAttribute>
</when>
<when test='$_event = "1"' >
<setEventAttribute attr="eventType" >Kaspersky CyberTrace service event</setEventAttribute>
</when>
</choose>
<collectFieldsByKeyValuePair kvsep="=" sep=";" src="$_body" >
<attrKeyMap attr="alertName" key="alert" />
<attrKeyMap attr="threatCategory" key="reason" />
<attrKeyMap attr="detectedIndicator" key="detected" />
<attrKeyMap attr="srcAction" key="act" />
<attrKeyMap attr="destIpAddr" key="dst" />
<attrKeyMap attr="srcIpAddr" key="src" />
<attrKeyMap attr="hashMD5" key="md5" />
<attrKeyMap attr="hashSHA1" key="sha1" />
<attrKeyMap attr="hashSHA2" key="sha2" />
<attrKeyMap attr="uriQuery" key="request" />
<attrKeyMap attr="dvcIpAddr" key="dvc" />
<attrKeyMap attr="serviceName" key="sourceServiceName" />
<attrKeyMap attr="user" key="suser" />
<attrKeyMap attr="msg" key="msg" />
</collectFieldsByKeyValuePair>
</parsingInstructions>
If you add new regular expressions and change the format of detection events in the kl_feed_service.conf configuration file, specify the new format of detection events in the Test Event field. Also, in the Parser XML field, in the
collectFieldsByKeyValuePairelement, add the correspondence rules between fields that are in the events from Kaspersky CyberTrace and FortiSIEM fields in which the values of the former fields must be stored. The correspondence rules must have the following format:<attrKeyMap attr="%FortiSIEM_field%" key="%Kaspersky_CyberTrace_field%" />.
Editing a parser definition
- Click the Reformat button.
- Click the Validate button to validate the XML data in the Parser XML field.
A message tells you whether the validation passed or failed.
- Click the Test button.
A window for testing the entered data opens.
- In the Test Event Parser window, click the Test button.
If error messages appear in the Errors column:
- Contact your technical account manager (TAM) to reconcile the contents of the Test Event field and the contents of the Parser XML field.
- Click Back and specify the correct data in the Test Event field and in the Parser XML field.
- Test the data again.
- Click Back.
- In the Event Parser Definition window, select the Enabled check box.
- Click Save.
- In the Admin > Device Support > Parser section, click Apply, and in the message box that opens click Yes to agree to the changes.
For more information about event parsers, visit http://help.fortinet.com/fsiem/5-1-1/Online-Help/HTML5_Help/Configuring_parsers.htm.
Page top