Allowing users to configure two-factor authentication
The two-factor authentication allowlist is a list of users who are permitted to initially configure two-factor authentication when signing in to Web Console. This list contains user accounts without configured two-factor authentication. By default, new user accounts are not included in the two-factor authentication allowlist and must be added to the list by an administrator. If a new account is an integration account used to run OpenAPI scripts, it must be excluded from two-factor authentication.
A user account will be automatically deleted from the two-factor authentication allowlist when it has configured two-factor authentication or is excluded from two-factor authentication.
Manual modifying the two-factor authentication allowlist is available for accounts that have configured two-factor authentication and that have the Modify object ACLs right in the General features: User permissions functional area.
To add a user account to the allow list manually:
- In the main menu, click the Administration Server name.
The Administration Server properties window opens.
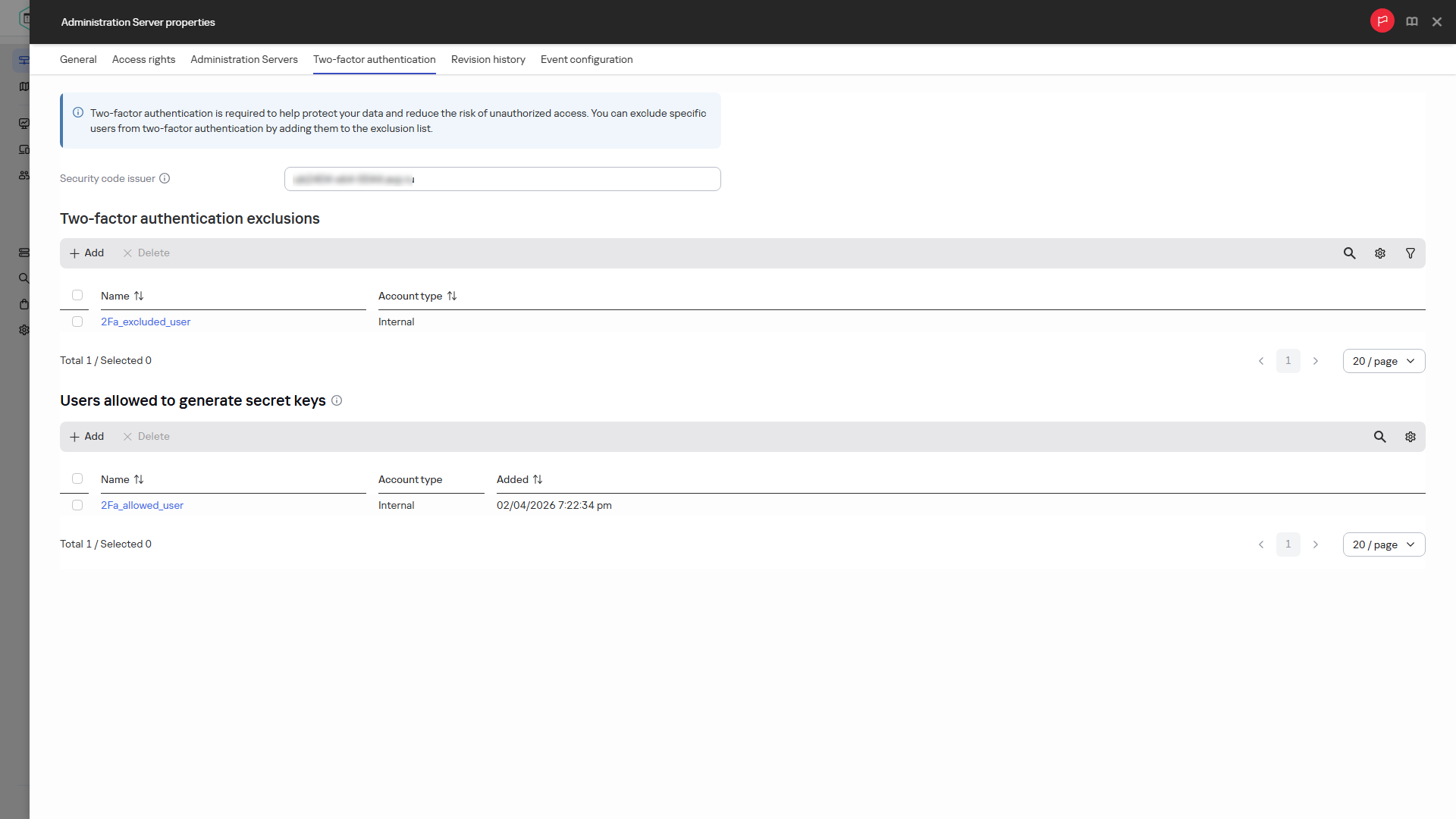
- On the Two-factor authentication tab of the properties window, in the Users allowed to generate secret keys table, click the Add button.
- In the window that opens:
- Select the user account that you want to add.
Only users who are not excluded from two-factor authentication and do not have a two-factor authentication secret key can be added to the allow list.
- If the account is protected against unauthorized modification, you must confirm that you have the permissions to change this account. In the Account protection window, specify the credentials of your own account and one-time security code for two-factor authentication.
- Save the changes.
- Select the user account that you want to add.
The selected user account is added to the two-factor authentication allowlist. At the next sign-in, the user will be able to generate a secret key.
A user account can be deleted from the two-factor authentication allowlist until two-factor authentication is configured for that account.
To delete user accounts from the two-factor authentication allowlist manually:
- In the main menu, click the Administration Server name.
The Administration Server properties window opens.
- On the Two-factor authentication tab of the properties window, in the Users allowed to generate secret keys table, select the user accounts that you want to delete, and then click Delete.
- If the account is protected against unauthorized modification, you must confirm that you have the permissions to change this account. In the Account protection window, specify the credentials of your own account and one-time security code for two-factor authentication.
The selected user accounts are deleted from the allow list.
Configuring the two-factor authentication allowlist
If, during an active session on Administration Server, your two-factor authentication secret key is deleted by another user or you reset the key yourself but do not create a new one, the ability to modify the allow list is blocked.
User accounts can also be automatically added and deleted from the two-factor authentication allowlist.
When resetting a two-factor authentication secret key for other accounts, their accounts are automatically added to the two-factor authentication allowlist so that they can generate a new secret key.
When upgrading Administration Server from version 16 or earlier to version 16.1 or later, as well as when you create a data backup on Administration Server 16 or earlier and restore it on Administration Server 16.1 or later, user accounts will be automatically added to the two-factor authentication allow list if all the following conditions are met:
- User has the Read permission in the functional area General features: Basic functionality assigned directly to the user (not through a security group). The scope of the user role with this permission must include all managed and unassigned devices, and must be set at the Administration Server level.
- User is not excluded from two-factor authentication.
- User does not have a two-factor authentication secret key.
- Two-factor authentication was not enabled for all users on Administration Server of the previous version.
Failure to meet even one condition will result in the user not being added to the two-factor authentication allowlist.
After an upgrade or restore, we recommend ensuring that the allow list contains only the user accounts that must have access to Administration Server. Review the allow list and remove any other accounts from it. Add integration accounts used to run scripts through OpenAPI to the exclusion list to prevent script failures.
Accounts of the users will lose access to Administration Server after an upgrade or restore if all the following conditions are met:
- User has the Read permission in the functional area General features: Basic functionality assigned through a security group (not directly to the user) or does not have this permission at all.
- User is not excluded from two-factor authentication.
- User does not have a two-factor authentication secret key.
- Two-factor authentication was enabled for all users on Administration Server of the previous version.
These accounts can be manually added to the two-factor authentication allowlist, if needed.
Page top