Installing EDR Agent
Kaspersky Endpoint Security in the Endpoint Detection and Response Agent (EDR Agent) configuration for Kaspersky Managed Detection and Response and Kaspersky Anti Targeted Attack Platform (EDR) solutions is installed in the same way.
EDR Agent can be installed on the computer in one of the following ways:
- Remotely using Kaspersky Security Center.
- Locally using the Setup Wizard.
- Locally on the command line (only for KATA (EDR)).
To install EDR Agent, you must select the appropriate configuration in installation package settings or in Setup Wizard.
How to install EDR Agent using the Setup Wizard
- Copy the distribution kit folder to the user's computer.
- Run setup_kes.exe.
The Setup Wizard starts.
Configuration of Kaspersky Endpoint Security
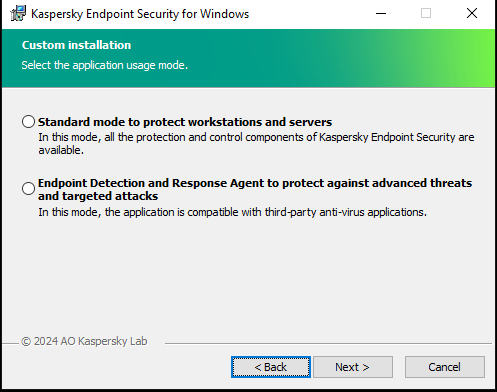
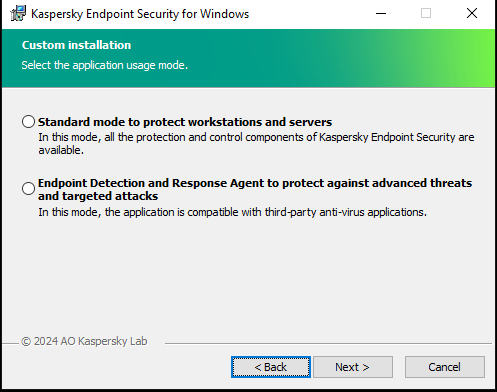
Choosing the configuration of the application
Select the Endpoint Detection and Response Agent configuration. In this configuration, you can only install the components that provide support for Detection and Response solutions: Endpoint Detection and Response (KATA) or Managed Detection and Response. This configuration is needed if a third-party Endpoint Protection Platform (EPP) is deployed in your organization alongside a Kaspersky Detection and Response solution. This makes Kaspersky Endpoint Security in the Endpoint Detection and Response Agent configuration compatible with third-party EPP applications.
Kaspersky Endpoint Security components
Select the components that you want to install (see figure below). You can change the available application components after the application is installed. To do so, you need to run the Setup Wizard again and choose to change the available components.
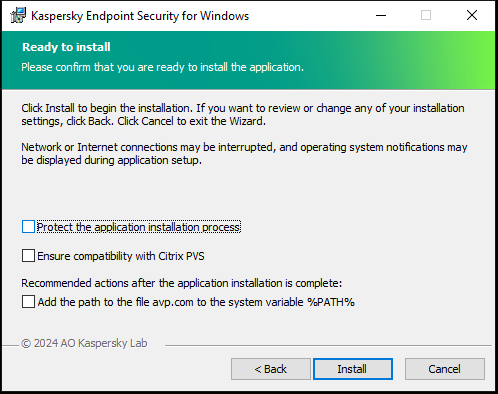
Advanced settings
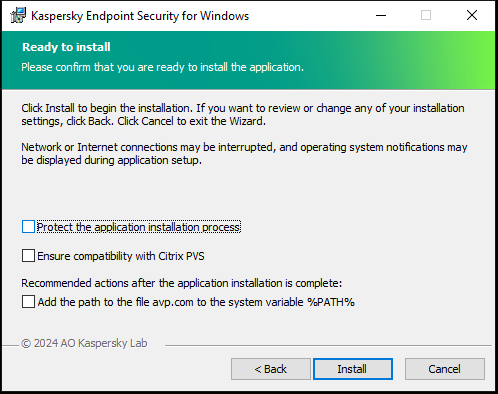
Advanced application installation settings
Protect the application installation process. Installation protection includes protection against replacement of the distribution package with malicious applications, blocking access to the installation folder of Kaspersky Endpoint Security, and blocking access to the system registry section containing application keys. However, if the application cannot be installed (for example, when performing remote installation with the help of Windows Remote Desktop), you are advised to disable protection of the installation process.
Ensure compatibility with Citrix PVS. You can enable support of Citrix Provisioning Services to install Kaspersky Endpoint Security to a virtual machine.
Add the path to the file avp.com to the system variable %PATH%. You can add the installation path to the %PATH% variable for convenient use of the command line interface.
How to install EDR Agent on the command line (only for KATA (EDR))
- Run the command line interpreter (cmd.exe) as an administrator.
- Go to the folder where the Kaspersky Endpoint Security distribution package is located.
- Run the following command:
setup_kes.exe /pEULA=1 /pPRIVACYPOLICY=1 /pKSN=1 /pSTANDALONEMODE=1 [/s]
or
msiexec /i <distribution kit name> EULA=1 PRIVACYPOLICY=1 KSN=1 STANDALONEMODE=1 [/qn]
As a result, the EDR Agent application for integration with Kaspersky Anti Targeted Attack Platform (EDR) is installed on the computer. You can confirm that application is installed and check application settings by issuing the status command.
How to install EDR Agent using the Administration Console (MMC)
- Open the Kaspersky Security Center Administration Console.
- In the console tree, select the Advanced → Remote installation → Installation packages folder.
This opens a list of installation packages that have been downloaded to Kaspersky Security Center.
- Open the properties of the installation package.
If necessary, create a new installation package.
- Go to the Settings section.
- Select the Endpoint Detection and Response Agent configuration. In this configuration, you can only install the components that provide support for Detection and Response solutions: Endpoint Detection and Response (KATA) or Managed Detection and Response. This configuration is needed if a third-party Endpoint Protection Platform (EPP) is deployed in your organization alongside a Kaspersky Detection and Response solution. This makes Kaspersky Endpoint Security in the Endpoint Detection and Response Agent configuration compatible with third-party EPP applications.
- Select the components that you want to install.
You can change the available application components after the application is installed.
- Save your changes.
- Create a remote installation task. In task properties, select the installation package you created.
How to install EDR Agent using Web Console
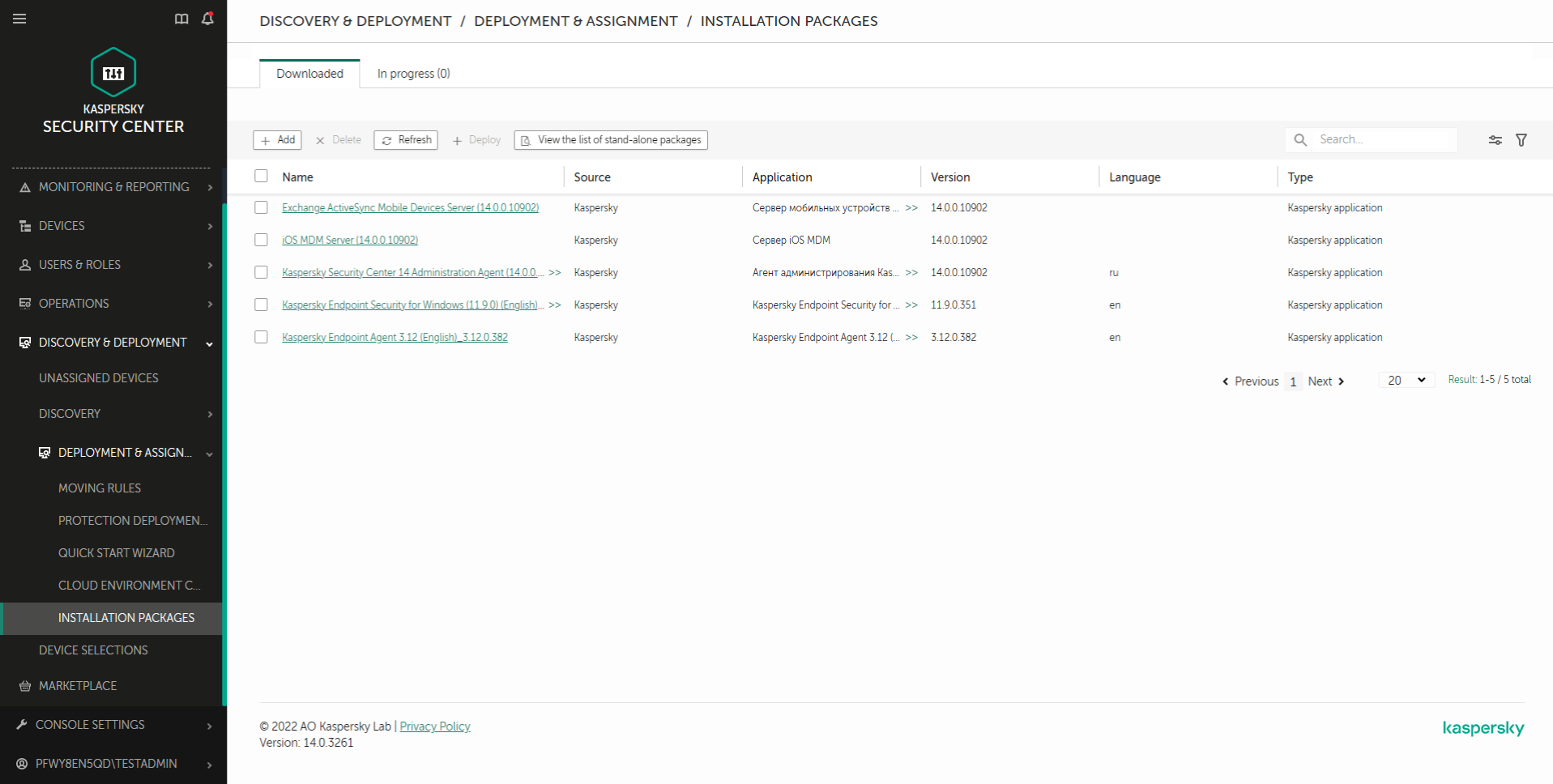
- In the main window of the Web Console, select Discovery & deployment → Deployment & assignment → Installation packages.
This opens a list of installation packages that have been downloaded to Kaspersky Security Center.
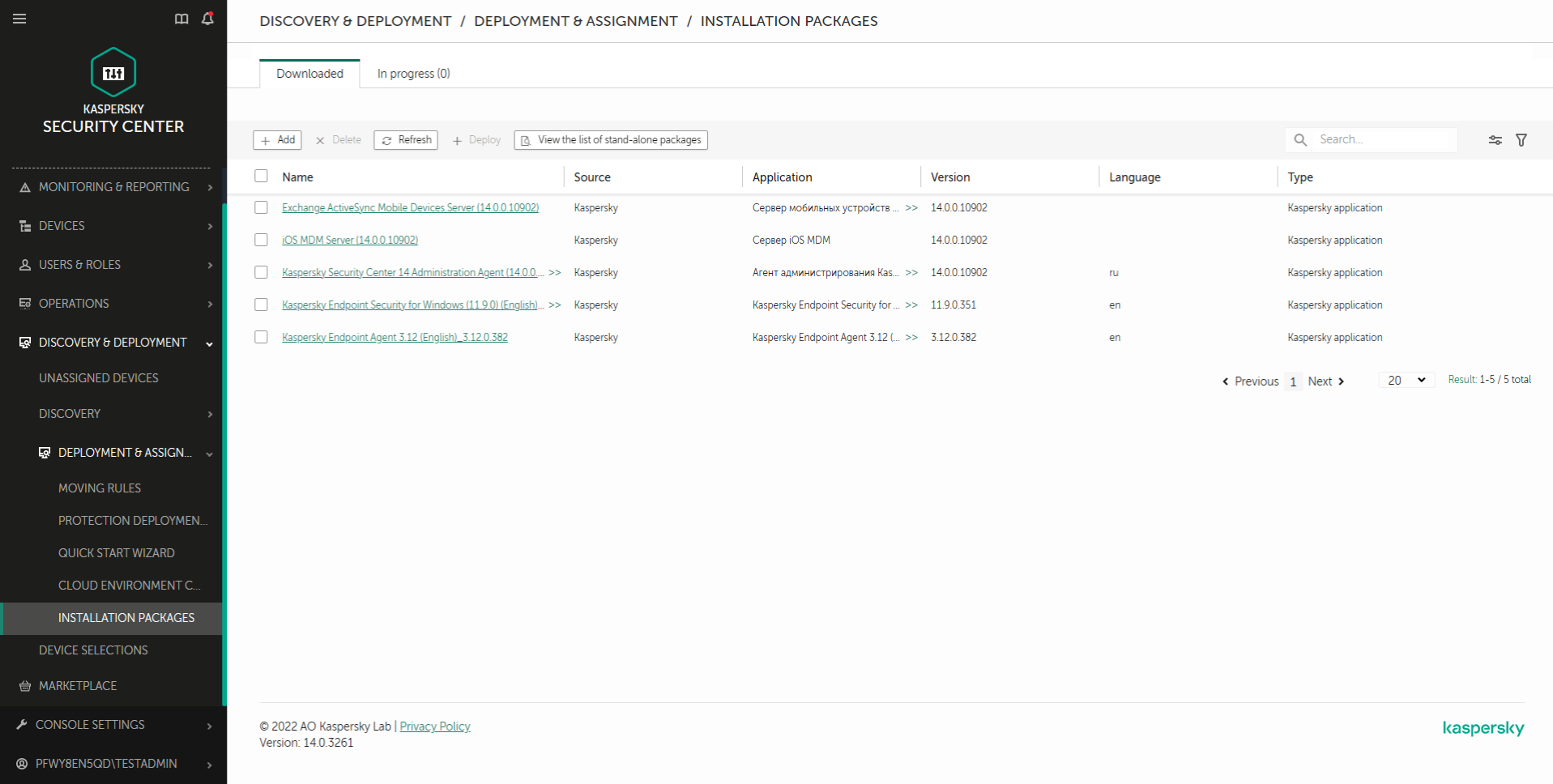
List of installation packages
- Open the properties of the installation package.
If necessary, create a new installation package.
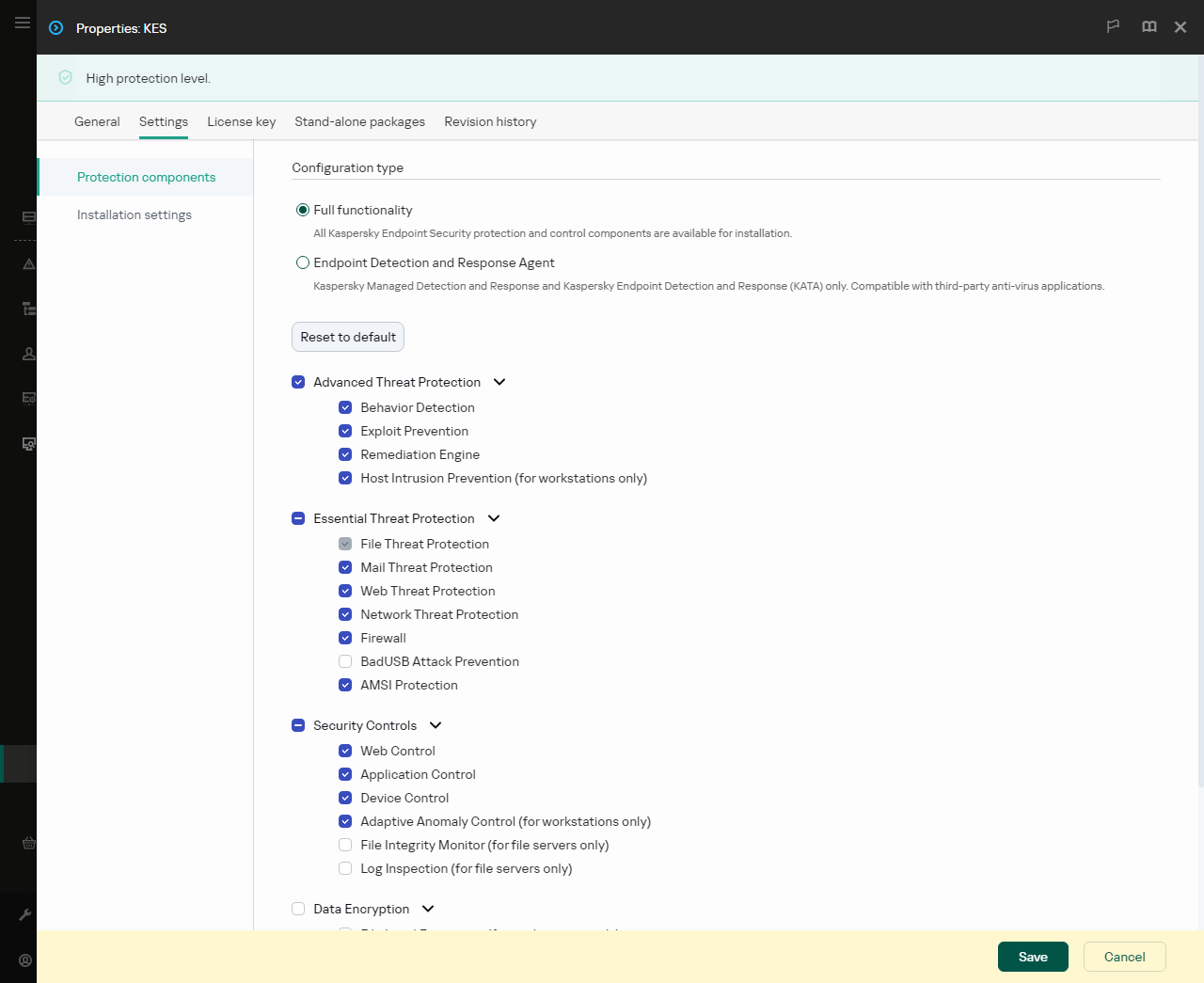
- Select the Settings tab.
- Go to the Protection components section.
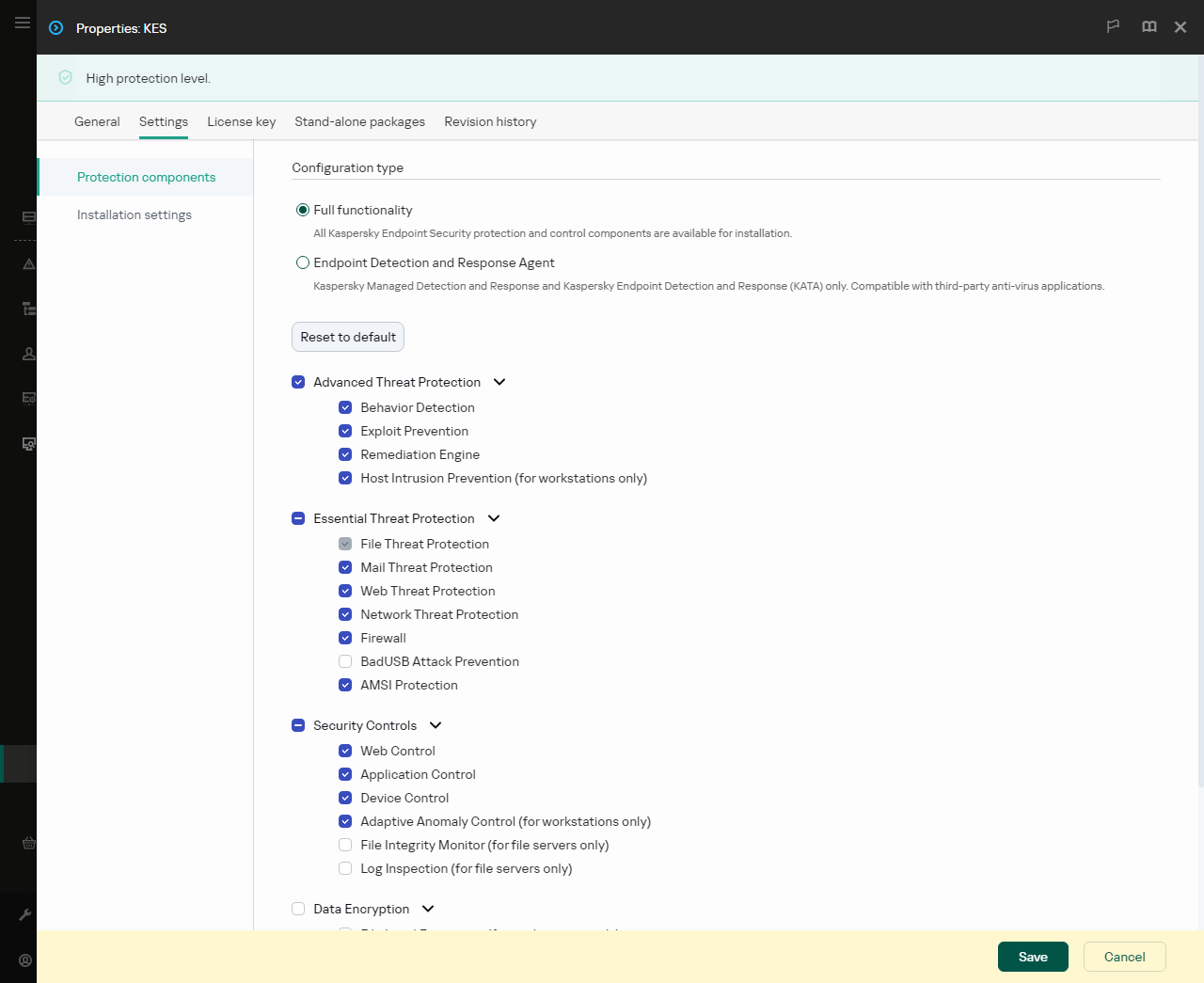
Components included in the installation package
- Select the Endpoint Detection and Response Agent to protect against advanced threats and targeted attacks configuration. In this configuration, you can only install the components that provide support for Detection and Response solutions: Endpoint Detection and Response (KATA) or Managed Detection and Response. This configuration is needed if a third-party Endpoint Protection Platform (EPP) is deployed in your organization alongside a Kaspersky Detection and Response solution. This makes Kaspersky Endpoint Security in the Endpoint Detection and Response Agent configuration compatible with third-party EPP applications.
- Select the components that you want to install.
You can change the available application components after the application is installed.
- Save your changes.
- Create a remote installation task. In task properties, select the installation package you created.
As a result, EDR Agent is installed on the user's computer. You can use the interface of the application and an icon of the application is displayed in the notification area  .
.
In Kaspersky Security Center, the computer with the installed application in the EDR Agent configuration has the Critical status –  . The computer has this status because the File Threat Protection component is missing. You do not need to take any action.
. The computer has this status because the File Threat Protection component is missing. You do not need to take any action.
If you could not install EDR Agent on a computer with a third-party EPP application because the installer found incompatible software on the computer, you can skip the incompatible software check.

Main window of EDR Agent
Now you must configure the integration with the Kaspersky Managed Detection and Response or Kaspersky Anti Targeted Attack (EDR) solution. You can also specify advanced settings of the application and, for example, create a trusted zone or hide the interface of the application. Settings in the following sections are available:
Page top
![]() .
. . The computer has this status because the File Threat Protection component is missing. You do not need to take any action.
. The computer has this status because the File Threat Protection component is missing. You do not need to take any action.