KATA integration dashboard
You can use the following methods to monitor the KATA integration status:
- View summary information about the state of the connection to the KATA server on all cluster nodes by checking the KATA Protection information pane in the Nodes section.
- View detailed information about the state of the connection to the KATA server on each cluster node.
- View information about the KATA server connection in the information window of each cluster node.
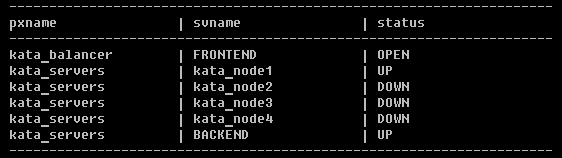
- Use a script to monitor the connection status of individual KATA servers in Technical Support Mode (when integrating with multiple servers of KATA version 5.0 or later).
The script requests the connection status from the built-in balancer and outputs it to the console.