How to protect your PC against file-encrypting ransomware
Ransomware is a kind of malware that encrypts your files and then demands ransom for decrypting them. Some ransomware encrypt files without demanding ransom.
Recommendations for reducing risks of ransomware infection
Install the protection solution
Kaspersky applications with the latest databases block attacks and prevent a malware from being installed on your computer. The latest versions of Kaspersky applications include the System Watcher component which automatically creates backup copies of files if a suspicious program tries to access them.
Install updates
Keep your software, operating systems and Kaspersky applications up-to-date. Especially check for patches that fix vulnerabilities on a regular basis. An updated software operates on the latest patch which limits the opportunities for attackers.
Updates improve the security, stability, and performance of your systems, help fix the latest vulnerabilities, and prevent attackers from exploiting them.
The software which is important to keep updated:
- Operating system patches
- Browser plug-ins
- VPN applications that provide access for remote employees and serve as a gateway to your network
Turn on all protection components and features of Kaspersky applications
All components and features of Kaspersky applications are aimed at ensuring the maximum protection of devices and reducing the risks of ransomware infection. Make sure that all components and features of your application are enabled and work properly.
Regularly back up your files and store them outside the PC
We recommend that you backup your data on a regular basis. Even in case of a successful ransomware or file-encrypting attack, the backup data will be recovered, reducing the negative impact of the attack. To protect your information against malware and computer damage, back up your files and store them on a removable drive or in a cloud storage.
Do not open attachments in emails from unknown senders
Ransomware spreads through infected files from emails. In such email letters, attackers pose as business partners or government officials, the subject lines and attachments contain important information, such as a notice of claim from the Arbitration Court and etc. Always check the sender’s address before opening emails and attachments.
Use strong passwords for Windows accounts when connecting remotely
Weak passwords can be easily guessed or cracked, giving attackers access to sensitive data. Use strong passwords to protect your personal data and your accounts from being hacked while connected remotely,
If you are using a public network, attackers can use Remote Desktop features for gaining access to your devices. Connect to Remote Desktop using only your home or corporate network. For more information about the Remote Desktop features, see the Microsoft support website.
Protect shared folders
Attackers can use shared folders for file-encrypting, spreading malware, and moving in the network of your organization. Kaspersky Endpoint Security for Windows protects shared folders from encryption and helps you set strong passwords.
Use Kaspersky Endpoint Detection and Response (KEDR) or Kaspersky Managed Detection and Response (MDR)
KEDR and MDR will detect and prevent an attack at the early stages. Using these solutions, you can identify and monitor suspicious signals.
Protect administrator accounts
Make sure administrator accounts are protected by strong passwords that are changed regularly (e.g., every 3 months). If possible, use two-step verification to minimize the risk of attackers gaining control of the network if they already have access to user credentials.
Monitor suspicious activity
Regularly check event logs and operational data for suspicious activity. Monitor lateral movements on the network and pay attention to outgoing traffic, as attackers usually need a connection to external networks or external tools to steal data.
Be cautious when using PowerShell
PowerShell is often used to attack Windows devices. Ransomware and fileless threats also use PowerShell to perform cyberattacks.
Limit the execution of PowerShell scripts. Disable execution of unassigned PowerShell scripts through politics. Enable the execution of PowerShell script only on accounts that need it. Do not change the PowerShell policy of restrictions (Set-ExecutionPolicy). Enable the Adaptive Anomaly Control component on devices protected by Kaspersky Endpoint Security for Windows and switch the Activity of Script Engine and Frameworks rule into the lock mode.
Configure policies
Configure policies to minimize the amount of network information available to users whose accounts can be compromised. The network information that can be retrieved by attackers from a breached device must be limited. It may limit the ability for cyberattacks, even if attackers managed to compromise an account or device, and prevent the privilege-escalation of the administrator or other devices, reducing the scale and impact of the attack.
Use IDS and IPS to detect and prevent network scans
The first step of a targeted attack is to collect information. Network scanning provides attackers with important information, such as open ports, active operating systems, software, and network device status. By preventing network scanning, you stop attackers from gathering important information and make it harder for them to attack.
Educate your employees and promote their awareness
- Be cautious with email attachments and check untrusted email addresses. Make sure the Mail Threat Protection component is enabled in Kaspersky Endpoint Security for Windows. The component scans computers and protects them against malicious attachments.
- Learn to recognize suspicious links sent in emails or other messaging platforms. Even if a link is sent by someone you know, they could have been hacked.
- Pay attention to suspicious activity on your devices or accounts. Log out of work systems when access to them is no longer required.
- Use strong passwords and two-factor authentication.
- Update personal operating systems and software regularly.
Kaspersky offers a special cybersecurity course: Automated Security Awareness Platform. It provides theoretical knowledge and builds cybersecurity skills.
Recommendations for configuring your computer
Create system restore points and back up your files
Regularly create system restore points and back up important files to a removable drive. This will allow you to restore the operating system to the uninfected state and restore files in case of infection or system malfunction.
For more information about backup and restore features, see Microsoft support website.
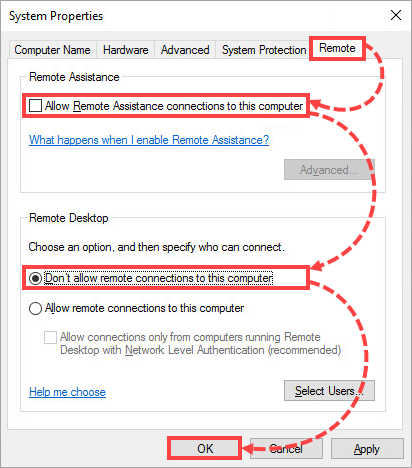
Deny remote connection to your computer
To prevent cybercriminals from remotely connecting to your computer, disallow this type of connection in the computer settings:
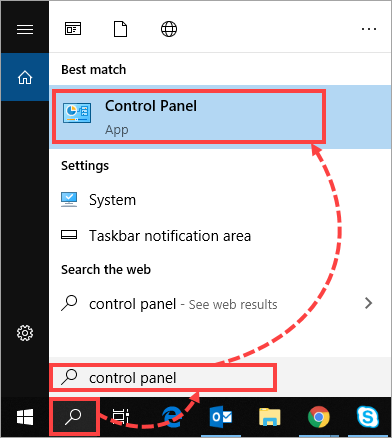
- Open Search and enter "control panel". Select Control Panel.
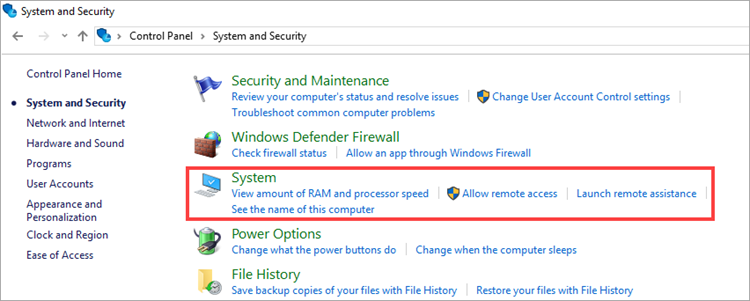
- Click System and Security and then select System.
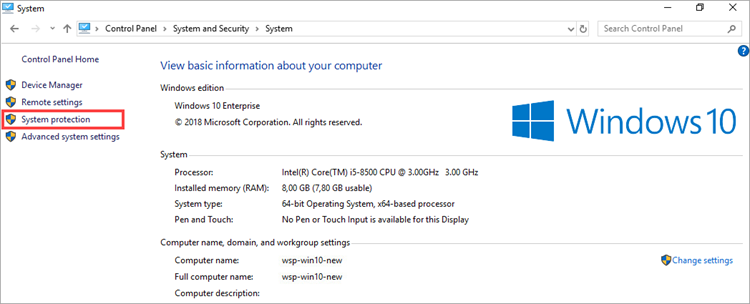
- Select System protection.
- Go to the Remote tab. Clear the Allow Remote Assistance connections to this computer check box and select Don't allow remote connections to this computer. Click ОК.
Recommendations on configuring Kaspersky applications
- Set a password for accessing a Kaspersky application:
- Enable the System Watcher feature in the Kaspersky application.
This feature blocks and rolls back malicious actions, detects and removes banners and creates backup copies of files upon suspicious access attempts. For instructions, see Online Help:
Recommendations on decrypting files
Try to restore the files
You can restore files using default Windows tools. See the instructions on the Microsoft support website.
Disable the automatic deletion of detected malicious files
If you have a Kaspersky application installed, open the application settings and clear the Perform recommended actions automatically check box in the General section.
We do not recommend removing infected files from quarantine as they may contain keys for decryption.
Send suspicious files for analysis
Contact Kaspersky Customer Service. Attach the encrypted file or email message to your request.
If you are using Kaspersky Endpoint Security for Windows, submit a request to Kaspersky Technical Support via Kaspersky CompanyAccount.
Kaspersky specialists cannot guarantee that the corrupted files will be decrypted.
Run a scan and remove the malware from your computer
Run a full scan of your computer to find the cause of infection and eliminate it. If you don’t have any protection solutions installed, use free Kaspersky tools: Kaspersky Free, Kaspersky Rescue Disk, or Kaspersky Virus Removal Tool.
What to do if there is a suspicious file on the computer
If you found a suspicious file that might have infected your computer or encrypted your files, follow one of the following actions:
- Scan files for known threats at Kaspersky Threat Intelligence Portal. If necessary, inform Kaspersky experts about a false detection or a new malicious software. To do so:
- Click Submit to reanalyze on the page with scan results.
- Enter your email address so we can contact you if necessary.
- Click Send.
- Contact Kaspersky Customer Service. Attach the suspicious file to your request and add the comment: “possible ransomware (cryptoransomware)”.
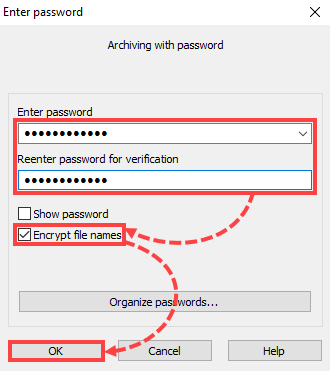
If you are using Kaspersky Endpoint Security for Windows, submit a request to Kaspersky Technical Support via Kaspersky CompanyAccount. - Send the files for analysis to newvirus@kaspersky.com. To do so, add the suspicious file to a ZIP or RAR archive using these instructions. Set the word “infected” as a password for the archive and select the check box Encrypt file names.
Possible ransomware file locations
- APPDATA
Windows NT/2000/XP — Drive:\Documents and Settings\%UserName%\Application Data\%USERPROFILE%\Local Settings\Application Data
Windows Vista/7/8/10 — Drive:\Users\%UserName%\AppData\Roaming\%USERPROFILE%\AppData\Local
- TEMP (temporary catalog)
%TEMP%\xxxxxxx.tmp\, where x stands for a—z characters or 0—9 numerals
%TEMP%\xxxxxxx.tmp\xx\, where x stands for a—z characters or 0—9 numerals
%TEMP%\xxxxxxx\, where x stands for a—z characters or 0—9 numerals
%WINDIR%\Temp
- Internet Explorer temporary files folder
Windows NT/2000/XP — %USERPROFILE%\Local Settings\Temporary Internet Files\
Windows Vista/7/8/10 — %LOCALAPPDATA%\Microsoft\Windows\Temporary Internet Files\content.ie5\xxxxxxxx, where x stands for a—z characters or 0—9 numerals
- Desktop
%UserProfile%\Desktop\
- Recycle bin
Disk:\Recycler\
Disk:\$Recycle.Bin\
Disk:\$Recycle.Bin\s-1-5-21-??????????-??????????-??????????-1000 (where ? stands for 0—9 numerals)
- System directory
%WinDir%
%SystemRoot%\system32\
- User's document folder
%USERPROFILE%\My documents\
%USERPROFILE%\My documents\Downloads
- Browser download folder
%USERPROFILE%\Downloads
- Startup folder
%USERPROFILE%\Start Menu\Programs\Startup