Standard installation of the application
Kaspersky Security Center provides a Protection Deployment Wizard for installing the application on corporate computers. The Protection Deployment Wizard includes the following main actions:
- Selecting a Kaspersky Endpoint Security installation package.
An installation package is a set of files created for remote installation of a Kaspersky application via Kaspersky Security Center. The installation package contains a range of settings needed to install the application and get it running immediately after installation. The installation package is created using files with the .kpd and .kud extensions included in the application distribution kit. Kaspersky Endpoint Security installation package is common for all supported Windows versions and processor architecture types.
- Creating the Install application remotely task of the Kaspersky Security Center Administration Server.
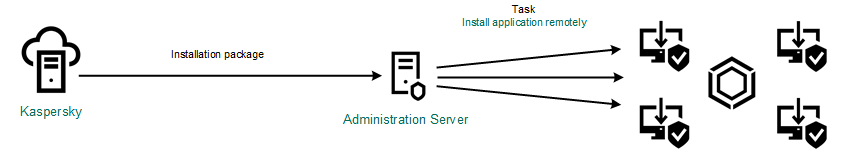
Kaspersky Endpoint Security deployment
How to run the Protection Deployment Wizard in the Administration Console (MMC)
- In the Administration Console, go to the folder Administration Server → Additional → Remote installation.
- Click the Deploy installation package on managed devices (workstations) link.
This will start the Protection Deployment Wizard. Follow the instructions of the Wizard.
TCP ports 139 and 445, and UDP ports 137 and 138 must be opened on a client computer.
Step 1. Selecting an installation package
Select Kaspersky Endpoint Security installation package from the list. If the list does not contain the installation package for Kaspersky Endpoint Security, you can create the package in the Wizard.
You can configure the installation package settings in Kaspersky Security Center. For example, you can select the application components that will be installed to a computer.
Network Agent will also be installed together with Kaspersky Endpoint Security. Network Agent facilitates interaction between the Administration Server and a client computer. If Network Agent is already installed on the computer, it is not installed again.
Step 2. Selecting devices for installation
Select the computers for installing Kaspersky Endpoint Security. The following options are available:
- Assign the task to an administration group. In this case, the task is assigned to computers included in a previously created administration group.
- Select computers detected by the Administration Server in the network: unassigned devices. Network Agent is not installed on unassigned devices. In this case, the task is assigned to specific devices. The specific devices can include devices in administration groups as well as unassigned devices.
- Specify device addresses manually, or import addresses from a list. You can specify NetBIOS names, IP addresses, and IP subnets of devices to which you want to assign the task.
Step 3. Defining remote installation task settings
Configure the following additional application settings:
- Force installation package download. Select the method of application installation:
- Using Network Agent. If Network Agent has not been installed on the computer, first Network Agent will be installed using the tools of the operating system. Then Kaspersky Endpoint Security is installed by the tools of Network Agent.
- Using operating system resources through distribution points. The installation package is delivered to client computers using operating system resources via distribution points. You can select this option if there is at least one distribution point in the network. For more details about distribution points, refer to the Kaspersky Security Center Help.
- Using operating system resources through Administration Server. Files will be delivered to client computers by using operating system resources through the Administration Server. You can select this option if Network Agent is not installed on the client computer, but the client computer is in the same network as the Administration Server.
- Behavior for devices managed through other Administration Servers. Select the Kaspersky Endpoint Security installation method. If the network has more than one Administration Server installed, these Administration Servers may see the same client computers. This may cause, for example, an application to be installed remotely on the same client computer several times through different Administration Servers, or other conflicts.
- Do not re-install application if it is already installed. Clear this check box if you want to install an earlier version of the application, for example.
- Assign Network Agent installation in Active Directory group policies. Manually installing Network Agent using Active Directory resources. To install Network Agent, the remote installation task must be run with domain administrator privileges.
Step 4. Selecting a license key
Add a key to the installation package for activating the application. This step is optional. If the Administration Server contains a license key with automatic distribution functionality, the key will be automatically added later. You can also activate the application later by using the Add key task.
Step 5. Selecting the operating system restart setting
Select the action to be performed if a computer restart is required. Restart is not required when installing Kaspersky Endpoint Security. Restart is required only if you have to remove incompatible applications prior to installation. Restart may also be required when updating the application version.
Step 6. Removing incompatible applications before installing the application
Carefully read the list of incompatible applications and allow removal of these applications. If incompatible applications are installed on the computer, installation of Kaspersky Endpoint Security ends with an error (see the figure below).
Step 7. Selecting an account for accessing devices
Select the account for installing Network Agent using the tools of the operating system. In this case, administrator rights are required for computer access. You can add multiple accounts. If an account does not have sufficient rights, the Installation Wizard uses the next account. If you install Kaspersky Endpoint Security using Network Agent tools, you do not have to select an account.
Step 8. Starting the installation
Exit the Wizard. If necessary, select the Run the task after the Wizard finishes check box. You can monitor the progress of the task in the task properties.
How to start the Protection Deployment Wizard in the Web Console and Cloud Console
In the main window of the Web Console, select Discovery & Deployment → Deployment & Assignment → Protection Deployment Wizard.
This will start the Protection Deployment Wizard. Follow the instructions of the Wizard.
TCP ports 139 and 445, and UDP ports 137 and 138 must be opened on a client computer.
Step 1. Selecting an installation package
Select Kaspersky Endpoint Security installation package from the list. If the list does not contain the installation package for Kaspersky Endpoint Security, you can create the package in the Wizard. To create the installation package, you do not need to search for the distribution package and save it to computer memory. In Kaspersky Security Center, you can view the list of distribution packages residing on Kaspersky servers, and the installation package is created automatically. Kaspersky updates the list after the release of new versions of applications.
You can configure the installation package settings in Kaspersky Security Center. For example, you can select the application components that will be installed to a computer.
Step 2. Selecting a license key
Add a key to the installation package for activating the application. This step is optional. If the Administration Server contains a license key with automatic distribution functionality, the key will be automatically added later. You can also activate the application later by using the Add key task.
Step 3. Selecting a Network Agent
Select the version of Network Agent that will be installed together with Kaspersky Endpoint Security. Network Agent facilitates interaction between the Administration Server and a client computer. If Network Agent is already installed on the computer, it is not installed again.
Step 4. Selecting devices for installation
Select the computers for installing Kaspersky Endpoint Security. The following options are available:
- Assign the task to an administration group. In this case, the task is assigned to computers included in a previously created administration group.
- Select computers detected by the Administration Server in the network: unassigned devices. Network Agent is not installed on unassigned devices. In this case, the task is assigned to specific devices. The specific devices can include devices in administration groups as well as unassigned devices.
- Specify device addresses manually, or import addresses from a list. You can specify NetBIOS names, IP addresses, and IP subnets of devices to which you want to assign the task.
Step 5. Configuring advanced settings
Configure the following additional application settings:
- Force installation package download. Selecting the method of application installation:
- Using Network Agent. If Network Agent has not been installed on the computer, first Network Agent will be installed using the tools of the operating system. Then Kaspersky Endpoint Security is installed by the tools of Network Agent.
- Using operating system resources through distribution points. The installation package is delivered to client computers using operating system resources via distribution points. You can select this option if there is at least one distribution point in the network. For more details about distribution points, refer to the Kaspersky Security Center Help.
- Using operating system resources through Administration Server. Files will be delivered to client computers by using operating system resources through the Administration Server. You can select this option if Network Agent is not installed on the client computer, but the client computer is in the same network as the Administration Server.
- Do not re-install application if it is already installed. Clear this check box if you want to install an earlier version of the application, for example.
- Assign package installation in Active Directory group policies. Kaspersky Endpoint Security is installed by means of Network Agent or manually by means of Active Directory. To install Network Agent, the remote installation task must be run with domain administrator privileges.
Step 6. Selecting the operating system restart setting
Select the action to be performed if a computer restart is required. Restart is not required when installing Kaspersky Endpoint Security. Restart is required only if you have to remove incompatible applications prior to installation. Restart may also be required when updating the application version.
Step 7. Removing incompatible applications before installing the application
Carefully read the list of incompatible applications and allow removal of these applications. If incompatible applications are installed on the computer, installation of Kaspersky Endpoint Security ends with an error (see the figure below).
Step 8. Assigning to an administration group
Select the administration group to which the computers will be moved after Network Agent is installed. Computers need to be moved to an administration group so that policies and group tasks can be applied. If a computer is already in any administration group, the computer will not be moved. If you do not select an administration group, computers will be added to the Unassigned devices group.
Step 9. Selecting an account for accessing devices
Select the account for installing Network Agent using the tools of the operating system. In this case, administrator rights are required for computer access. You can add multiple accounts. If an account does not have sufficient rights, the Installation Wizard uses the next account. If you install Kaspersky Endpoint Security using Network Agent tools, you do not have to select an account.
Step 10. Starting installation
Exit the Wizard. If necessary, select the Run the task after the Wizard finishes check box. You can monitor the progress of the task in the task properties.