Kaspersky Endpoint Security for Windows 11.3.0
- Čeština (Česká republika)
- Deutsch
- Español (España)
- Español (México)
- Français
- Italiano
- Magyar (Magyarország)
- Polski (Polska)
- Português (Brasil)
- Português (Portugal)
- Română (România)
- Tiếng Việt (Việt Nam)
- Türkçe (Türkiye)
- Русский
- العربية (الإمارات العربية المتحدة)
- 한국어 (대한민국)
- 简体中文
- 繁體中文
- 日本語(日本)
- Čeština (Česká republika)
- Deutsch
- Español (España)
- Español (México)
- Français
- Italiano
- Magyar (Magyarország)
- Polski (Polska)
- Português (Brasil)
- Português (Portugal)
- Română (România)
- Tiếng Việt (Việt Nam)
- Türkçe (Türkiye)
- Русский
- العربية (الإمارات العربية المتحدة)
- 한국어 (대한민국)
- 简体中文
- 繁體中文
- 日本語(日本)
- Frequently asked questions
- What's new
- Kaspersky Endpoint Security for Windows
- Installing and removing the application
- Deployment through Kaspersky Security Center
- Installing the application using the Wizard
- Installing the application from the command line
- Remotely installing the application using System Center Configuration Manager
- Description of setup.ini file installation settings
- Changing application components
- Upgrading from a previous version of the application
- Removing the application
- Application licensing
- Managing the application via the local interface
- Application interface
- Starting and stopping the application
- Scanning the computer
- Starting or stopping a scan task
- Changing the security level
- Changing the action to take on infected files
- Generating a list of objects to scan
- Selecting the type of files to scan
- Optimizing file scanning
- Scanning compound files
- Using scan methods
- Using scan technologies
- Selecting the run mode for the scan task
- Starting a scan task under the account of a different user
- Scanning removable drives when they are connected to the computer
- Background scan
- Updating databases and application software modules
- Adding an update source
- Selecting the update server region
- Configuring updates from a shared folder
- Selecting the update task run mode
- Starting an update task under the rights of a different user account
- Configuring application module updates
- Starting and stopping an update task
- Last update rollback
- Configuring proxy server use
- Working with active threats
- Kaspersky Security Network
- Behavior Detection
- Exploit Prevention
- Host Intrusion Prevention
- Limitations of audio and video device control
- Enabling and disabling Host Intrusion Prevention
- Managing application trust groups
- Managing application rights
- Changing application rights for trust groups and groups of applications
- Modifying application rights
- Disabling downloads and updates of application rights from the Kaspersky Security Network database
- Disabling the inheritance of restrictions from the parent process
- Excluding specific application actions from application rights
- Deleting information about unused applications
- Protecting operating system resources and identity data
- Remediation Engine
- File Threat Protection
- Enabling and disabling File Threat Protection
- Automatic pausing of File Threat Protection
- Changing the security level
- Changing the action taken on infected files by the File Threat Protection component
- Forming the protection scope of the File Threat Protection component
- Using heuristic analysis in the operation of the File Threat Protection component
- Using scan technologies in the operation of the File Threat Protection component
- Optimizing file scanning
- Scanning compound files
- Changing the scan mode
- Web Threat Protection
- Enabling and disabling Web Threat Protection
- Changing the web traffic security level
- Changing the action to take on malicious web traffic objects
- Using Web Threat Protection to check links against databases of phishing and malicious web addresses
- Using heuristic analysis in the operation of the Web Threat Protection component
- Creating the list of trusted web addresses
- Mail Threat Protection
- Enabling and disabling Mail Threat Protection
- Changing the mail security level
- Changing the action to take on infected email messages
- Forming the protection scope of the Mail Threat Protection component
- Scanning compound files attached to email messages
- Filtering email message attachments
- Scanning emails in Microsoft Office Outlook
- Network Threat Protection
- Firewall
- BadUSB Attack Prevention
- AMSI Protection Provider
- Application Control
- Device Control
- Enabling and disabling Device Control
- About access rules
- Editing a device access rule
- Adding or excluding records to or from the event log
- Adding a Wi-Fi network to the trusted list
- Editing a connection bus access rule
- Actions with trusted devices
- Obtaining access to a blocked device
- Editing templates of Device Control messages
- Anti-Bridging
- Web Control
- Enabling and disabling Web Control
- Actions with web resource access rules
- Migrating web resource access rules from previous versions of the application
- Exporting and importing the list of web resource addresses
- Monitoring user Internet activity
- Editing masks for web resource addresses
- Editing templates of Web Control messages
- Adaptive Anomaly Control
- Enabling and disabling Adaptive Anomaly Control
- Enabling and disabling an Adaptive Anomaly Control rule
- Modifying the action taken when an Adaptive Anomaly Control rule is triggered
- Creating and editing an exclusion for an Adaptive Anomaly Control rule
- Deleting an Adaptive Anomaly Control rule exclusion
- Importing exclusions for Adaptive Anomaly Control rules
- Exporting exclusions for Adaptive Anomaly Control rules
- Applying updates for Adaptive Anomaly Control rules
- Editing Adaptive Anomaly Control message templates
- Viewing Adaptive Anomaly Control reports
- Network Protection
- Checking the integrity of application modules
- Password protection
- Notification service
- Managing reports
- Managing Backup
- Trusted zone
- Kaspersky Endpoint Security Self-Defense
- Kaspersky Endpoint Security performance and compatibility with other applications
- Creating and using a configuration file
- Managing the application via the Kaspersky Security Center Administration Console
- Special considerations when working with different versions of management plug-ins
- Starting and stopping Kaspersky Endpoint Security on a client computer
- Configuring Kaspersky Endpoint Security settings
- Managing Tasks
- Managing policies
- Data Encryption
- Encryption functionality limitations
- Changing the length of the encryption key (AES56 / AES256)
- Full Disk Encryption
- Full disk encryption using Kaspersky Disk Encryption technology
- Full disk encryption using BitLocker Drive Encryption technology
- Creating a list of hard drives excluded from encryption
- Hard drive decryption
- Restoring access to a drive protected by Kaspersky Disk Encryption technology
- Restore access to a drive encrypted with BitLocker
- Updating the operating system
- Eliminating errors of encryption functionality update
- File Level Encryption on local computer drives
- Encrypting files on local computer drives
- Forming encrypted file access rules for applications
- Encrypting files that are created or modified by specific applications
- Generating a decryption rule
- Decrypting files on local computer drives
- Creating encrypted packages
- Restoring access to encrypted files
- Restoring access to encrypted data after operating system failure
- Editing templates of encrypted file access messages
- Encryption of removable drives
- Using the Authentication Agent
- Enabling Single Sign-On (SSO) technology
- Managing Authentication Agent accounts
- Using a token and smart card with Authentication Agent
- Selecting the Authentication Agent tracing level
- Editing Authentication Agent help texts
- Removing leftover objects and data after testing the operation of Authentication Agent
- Viewing data encryption details
- Working with encrypted devices when there is no access to them
- Application Control
- Managing Application Control rules
- Receiving information about the applications that are installed on users’ computers
- Creating application categories
- Adding executable files from the Executable files folder to the application category
- Adding event-related executable files to the application category
- Adding and modifying an Application Control rule using Kaspersky Security Center
- Changing the status of an Application Control rule via Kaspersky Security Center
- Testing Application Control rules using Kaspersky Security Center
- Viewing events resulting from test operation of the Application Control component
- Viewing a report on blocked applications in test mode
- Viewing events resulting from operation of the Application Control component
- Viewing a report on blocked applications
- Best practices for implementing white list mode
- Managing Application Control rules
- Sending user messages to the Kaspersky Security Center server
- Viewing user messages in the Kaspersky Security Center event storage
- Remote administration of the application through Kaspersky Security Center Web Console and Cloud Console
- About Kaspersky Endpoint Security management web plug-in
- Getting started
- Starting and stopping Kaspersky Endpoint Security
- Updating databases and application software modules
- Managing Tasks
- Managing policies
- Configuring local application settings
- Policy settings
- Kaspersky Security Network
- Behavior Detection
- Exploit Prevention
- Host Intrusion Prevention
- Remediation Engine
- File Threat Protection
- Web Threat Protection
- Mail Threat Protection
- Network Threat Protection
- Firewall
- BadUSB Attack Prevention
- AMSI Protection Provider
- Application Control
- Device Control
- Web Control
- Adaptive Anomaly Control
- Full Disk Encryption
- File Level Encryption
- Encryption of removable drives
- Templates (data encryption)
- Endpoint Sensor
- Managing Tasks
- Scan from context menu
- Removable drives scan
- Background scan
- Application settings
- Network options
- Exclusions
- Reports and Storage
- Interface
- Managing the application from the command line
- Commands
- SCAN. Virus Scan
- UPDATE. Updating databases and application software modules
- ROLLBACK. Last update rollback
- TRACES. Tracing
- START. Start the profile
- STOP. Stopping a profile
- STATUS. Profile status
- STATISTICS. Profile operation statistics
- RESTORE. Restoring files
- EXPORT. Exporting application settings
- IMPORT. Importing application settings
- ADDKEY. Applying a key file.
- LICENSE. Licensing
- RENEW. Purchasing a license
- PBATESTRESET. Reset the disk check results before encrypting the disk
- EXIT. Exit the application
- EXITPOLICY. Disabling policy
- STARTPOLICY. Enabling policy
- DISABLE. Disabling protection
- SPYWARE. Spyware detection
- KESCLI commands
- Scan. Virus Scan
- GetScanState. Scan completion status
- GetLastScanTime. Determining the scan completion time
- GetThreats. Obtaining data on detected threats
- UpdateDefinitions. Updating databases and application software modules
- GetDefinitionState. Determining the update completion time
- EnableRTP. Enabling protection
- GetRealTimeProtectionState. File Threat Protection status
- Version. Identifying the application version
- Error codes
- Appendix. Application profiles
- Commands
- Managing the application through the REST API
- Integration with other Kaspersky solutions
- Sources of information about the application
- Contacting Technical Support
- Glossary
- Active key
- Administration group
- Anti-virus databases
- Archive
- Authentication Agent
- Certificate issuer
- Database of malicious web addresses
- Database of phishing web addresses
- Disinfection
- False alarm
- Infected file
- License certificate
- Mask
- Network Agent
- Normalized form of the address of a web resource
- OLE object
- Portable File Manager
- Protection scope
- Reserve key
- Scan scope
- Task
- Trusted Platform Module
- Appendix 1. Application trust groups
- Appendix 2. Web resource content categories
- Information about third-party code
- Trademark notices
Device Control
This component is available if Kaspersky Endpoint Security is installed on a computer that runs on Windows for workstations. This component is unavailable if Kaspersky Endpoint Security is installed on a computer that runs on Windows for servers.
Device Control manages user access to devices that are installed on or connected to the computer (for example, hard drives, cameras, or Wi-Fi modules). This lets you protect the computer from infection when such devices are connected, and prevent loss or leaks of data.
Device access levels
Device Control controls access at the following levels:
- Device type. For example, printers, removable drives, and CD/DVD drives.
You can configure device access as follows:
- Allow –
 .
. - Block –
 .
. - Depends on connection bus (except for Wi-Fi) –
 .
. - Block with exceptions (only Wi-Fi and portable devices (MTP) –
 .
.
- Allow –
- Connection bus. A connection bus is an interface used for connecting devices to the computer (for example, USB or FireWire). Therefore, you can restrict the connection of all devices, for example, over USB.
You can configure device access as follows:
- Allow –
 .
. - Block –
 .
.
- Allow –
- Trusted devices. Trusted devices are devices to which users that are specified in the trusted device settings have full access at all times.
You can add trusted devices based on the following data:
- Devices by ID. Each device has a unique identifier (Hardware ID, or HWID). You can view the ID in the device properties by using operating system tools. Example device ID:
SCSI\CDROM&VEN_NECVMWAR&PROD_VMWARE_SATA_CD00\5&354AE4D7&0&000000. Adding devices by ID is convenient if you want to add several specific devices. - Devices by model. Each device has a vendor ID (VID) and a product ID (PID). You can view the IDs in the device properties by using operating system tools. Template for entering the VID and PID:
VID_1234&PID_5678. Adding devices by model is convenient if you use devices of a certain model in your organization. This way, you can add all devices of this model. - Devices by ID mask. If you are using multiple devices with similar IDs, you can add devices to the trusted list by using masks. The
*character replaces any set of characters. Kaspersky Endpoint Security does not support the?character when entering a mask. For example,WDC_C*. - Devices by model mask. If you are using multiple devices with similar VIDs or PIDs (for example, devices from the same manufacturer), you can add devices to the trusted list by using masks. The
*character replaces any set of characters. Kaspersky Endpoint Security does not support the?character when entering a mask. For example,VID_05AC & PID_ *.
- Devices by ID. Each device has a unique identifier (Hardware ID, or HWID). You can view the ID in the device properties by using operating system tools. Example device ID:
Device Control regulates user access to devices by using access rules. Device Control also lets you save device connection/disconnection events. To save events, you need to configure the registration of events in a policy.
If access to a device depends on the connection bus (the ![]() status), Kaspersky Endpoint Security does not save device connection/disconnection events. To enable Kaspersky Endpoint Security to save device connection/disconnection events, allow access to the corresponding type of device (the
status), Kaspersky Endpoint Security does not save device connection/disconnection events. To enable Kaspersky Endpoint Security to save device connection/disconnection events, allow access to the corresponding type of device (the ![]() status) or add the device to the trusted list.
status) or add the device to the trusted list.
When a device that is blocked by Device Control is connected to the computer, Kaspersky Endpoint Security will block access and show a notification (see the figure below).
Device Control notification
Device Control operating algorithm
Kaspersky Endpoint Security makes a decision on whether to allow access to a device after the user connects the device to the computer (see the figure below).
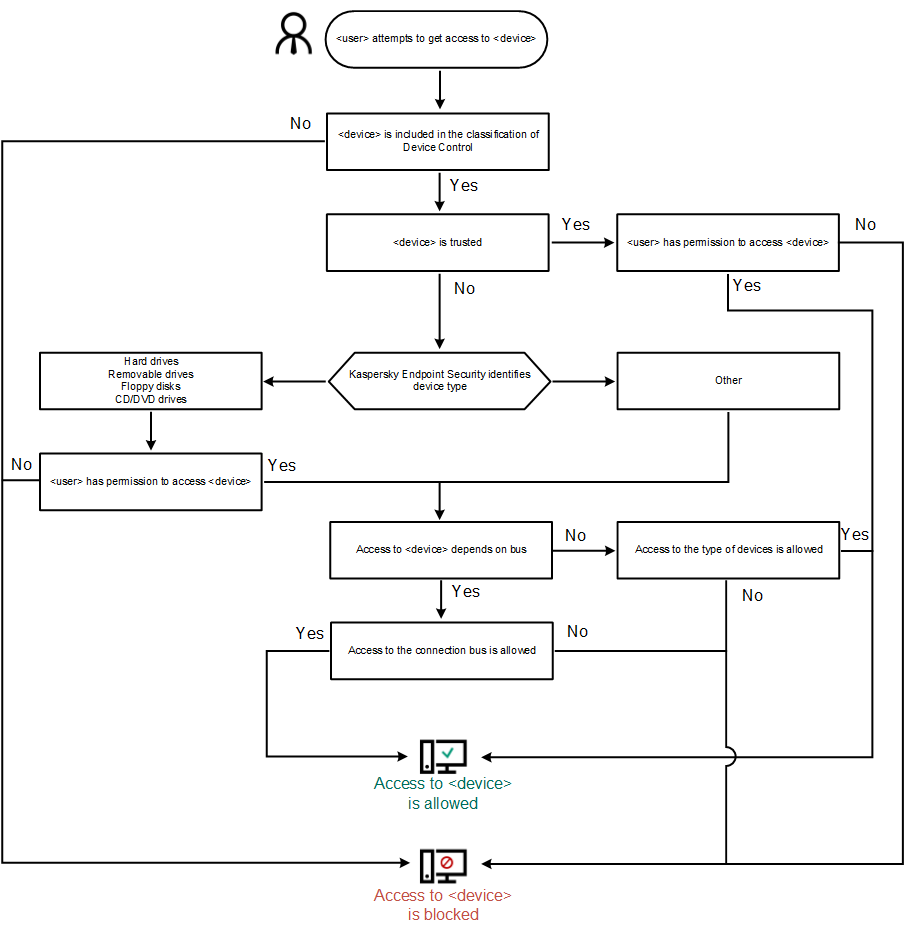
Device Control operating algorithm
If a device is connected and access is allowed, you can edit the access rule and block access. In this case, the next time someone attempts to access the device (such as to view the folder tree, or perform read or write operations), Kaspersky Endpoint Security blocks access. A device without a file system is blocked only the next time that the device is connected.
If a user of the computer with Kaspersky Endpoint Security installed must request access to a device that the user believes was blocked by mistake, send the user the request access instructions.