Pausing BitLocker protection to update software
There are a number of special considerations for updating the operating system, installing update packages for the operating system, or updating other software with BitLocker protection turned on. Installing updates may require restarting the computer multiple times. After each restart, the user must complete BitLocker authentication. To make sure updates install correctly, you can temporarily turn off BitLocker authentication. In this case the disk stays encrypted and the user has access to data after signing in to the system. To manage BitLocker authentication, you can use the BitLocker Protection Management task. You can use this task to specify the number of computer restarts that do not require BitLocker authentication. In this way, after updates are installed and the BitLocker Protection Management task is complete, BitLocker authentication is automatically enabled. You can enable BitLocker authentication at any time.
How to pause BitLocker protection using the Administration Console (MMC)
- Open the Kaspersky Security Center Administration Console.
- In the console tree, select Tasks.
The list of tasks opens.
- Click New task.
The Task Wizard starts. Follow the instructions of the Wizard.
Step 1. Selecting task type
Select Kaspersky Endpoint Security for Windows (12.8) → BitLocker Protection Management.
Step 2. BitLocker Protection Management
Configure BitLocker authentication. To pause BitLocker protection, select Temporarily allow skipping BitLocker authentication and enter the number of restarts without BitLocker authentication (1 to 15 times). If necessary, enter an expiration date and time for the task. At the specified time, the task is automatically turned off, and the user must complete BitLocker authentication when the computer is restarted.
Step 3. Selecting the devices to which the task will be assigned
Select the computers on which the task will be performed. The following options are available:
- Assign the task to an administration group. In this case, the task is assigned to computers included in a previously created administration group.
- Select computers detected by the Administration Server in the network: unassigned devices. The specific devices can include devices in administration groups as well as unassigned devices.
- Specify device addresses manually, or import addresses from a list. You can specify NetBIOS names, IP addresses, and IP subnets of devices to which you want to assign the task.
Step 4. Defining the task name
Enter the name of the task, for example Updating to Windows 10.
Step 5. Completing task creation
Exit the Wizard. If necessary, select the Run the task after the wizard finishes check box. You can monitor the progress of the task in the task properties.
How to pause BitLocker protection using Web Console
- In the main window of the Web Console, select Assets (Devices) → Tasks.
The list of tasks opens.
- Click Add.
The Task Wizard starts. Follow the instructions of the Wizard.
Step 1. Configuring general task settings
Configure the general task settings:
- In the Application drop-down list, select Kaspersky Endpoint Security for Windows (12.8.0).
- In the Task type drop-down list, select BitLocker protection management.
- In the Task name field, enter a brief description, for example, Updating to Windows 10.
- In the Devices to which the task will be assigned block, select the task scope.
Step 2. BitLocker Protection Management
Configure BitLocker authentication. To pause BitLocker protection, select Temporarily allow skipping BitLocker authentication and enter the number of restarts without BitLocker authentication (1 to 15 times). If necessary, enter an expiration date and time for the task. At the specified time, the task is automatically turned off, and the user must complete BitLocker authentication when the computer is restarted.
Step 3. Completing task creation
Exit the Wizard. A new task will be displayed in the list of tasks.
To run a task, select the check box opposite the task and click the Start button.
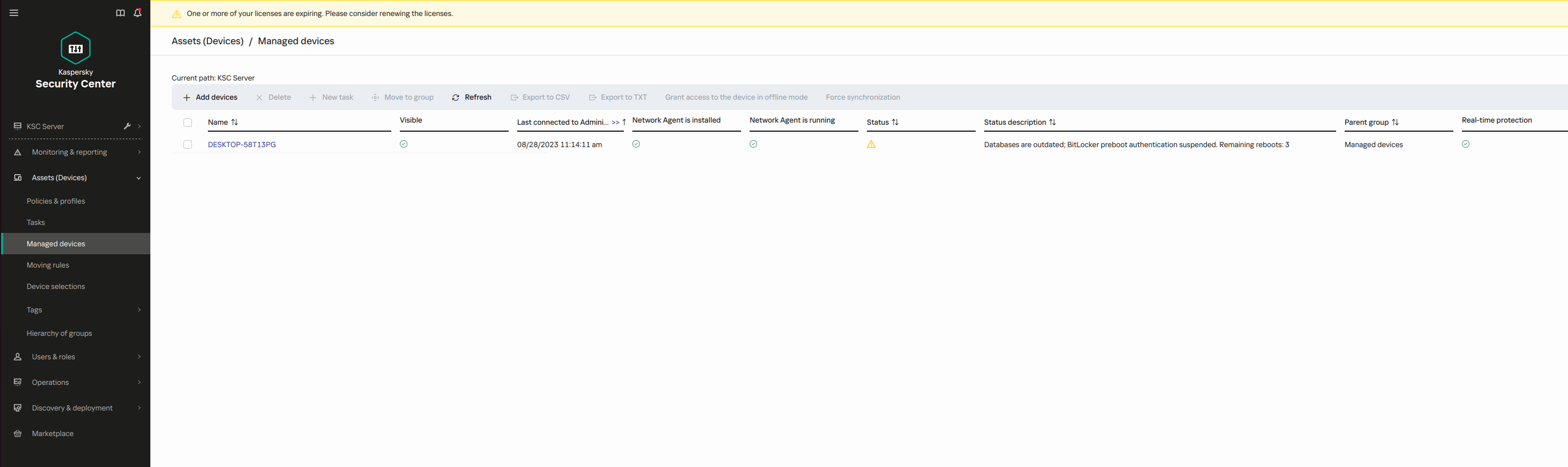
As a result, when the task is running, after the next restart of the computer, BitLocker does not prompt the user for authentication. After each restart of the computer without BitLocker authentication, Kaspersky Endpoint Security generates a corresponding event and records the number of remaining restarts. Kaspersky Endpoint Security then sends the event to Kaspersky Security Center to be monitored by the administrator. You can also view the number of remaining restarts in the Managed devices folder of Kaspersky Security Center console in the device status description.
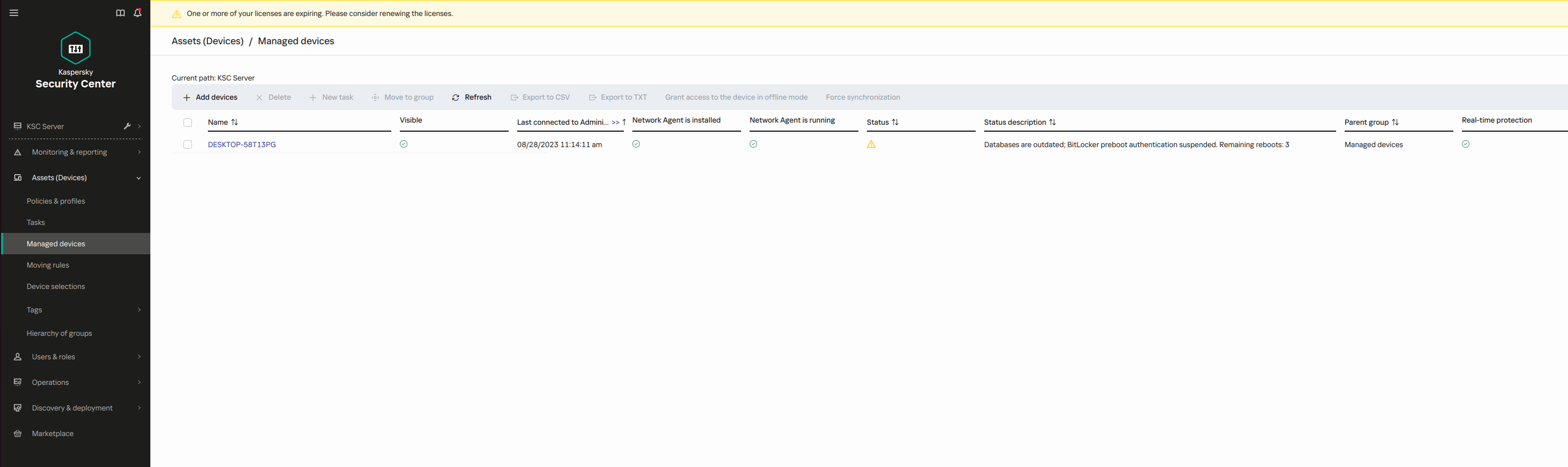
The list of managed devices
When the specified number of restarts or the expiration time of the task is reached, BitLocker authentication is automatically turned on. To gain access to data, the user must complete BitLocker authentication.
On computers running Windows 7, BitLocker cannot count computer restarts. Counting restarts on Windows 7 computers is handled by Kaspersky Endpoint Security. Thus to automatically turn on BitLocker authentication after each restart, Kaspersky Endpoint Security must be started.
To turn on BitLocker authentication ahead of time, open the BitLocker Protection Management task properties and select Request authentication each time in preboot.
Page top