Creating notifications about incoming service events
You can create notifications about incoming Kaspersky CyberTrace service events by configuring alert rules.
To create notifications about service events from Kaspersky CyberTrace in ArcSight ESM:
- Run ArcSight Console.
- In the Navigator pane, select Rules in the drop-down-list.
- In the tree view, select the Rules > Shared > All Rules > Public directory.
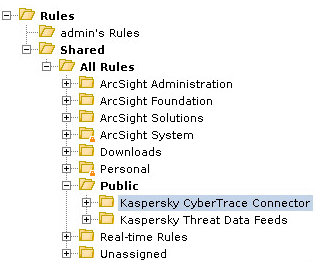
The Rules tree view
- Right-click the filter node in the Kaspersky CyberTrace Connector tree and select New Rule > Standard Rule.
- In the Inspect > Edit pane, specify the following settings:
- In the Name field of the Attributes tab, specify the name of the rule.
You can specify any name.
- On the Conditions tab, specify the following conditions:
Device Product = Kaspersky CyberTrace for ArcSightReason = %ServiceEventCode%Where
%ServiceEventCode%is a code of a service event that is used for generating notifications.
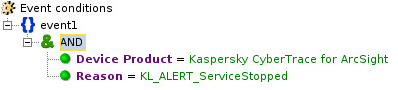
Event conditions
- Right-click the Actions tab, choose On Every Event and then select the following:
- Activate Trigger
- Add
This setting must contain the action that will be performed when a service event that is specified on the Conditions tab is received. For example, Send Notification.
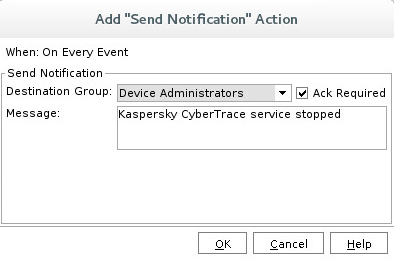
Adding actions
- In the Name field of the Attributes tab, specify the name of the rule.
- Click Apply.