Allowlists and denylists
You can use allowlists and denylists for more granular control of the way the mail system reacts to messages from certain addresses. For example, sources that are officially not spam but are identified by the application as mass mail (for example, messages from news portals) can be added to the allowlist.
You can use the following to configure allowlists and denylists:
- Preset AllowList and DenyList message processing rules. You can also create your own rules with sender and recipient addresses to whose messages the specified action must be applied, and change the priorities of the rules.
By default, AllowList and DenyList rules are turned off, and no sender and recipient addresses are specified therein. You will have to generate address lists in these rules and turn on the rules.
- Personal allowlists and denylists that contain sender addresses for a single recipient. A personal allowlist allows messages to pass through without Anti-Spam scans. The messages are still scanned for phishing, viruses, and other threats, and content filtering is also performed.
A flowchart of the default algorithm for processing messages in accordance with allowlists and denylists is shown in the figure below. You can change the action for the DenyList rule (Reject or Delete message) as well as change the rules priority by moving the AllowList and DenyList rules around the rule table. In this case, the algorithm for applying actions will differ from the one described below.
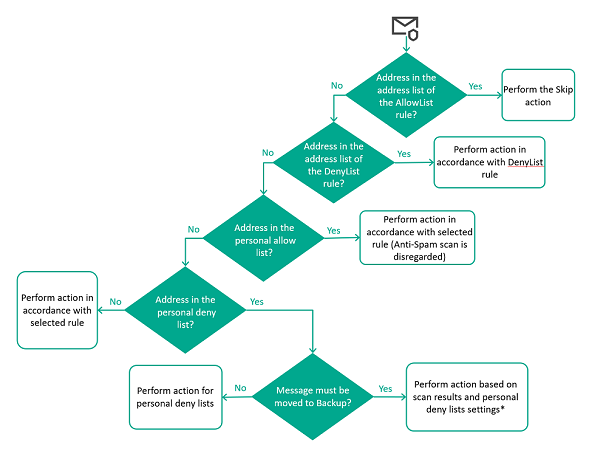
Algorithm for processing messages in accordance with allowlists and denylists
Messages whose sender and recipients have their addresses on an allowlist or denylist in message processing rules are processed as follows:
- If the addresses of the sender and recipients of a message are on the allowlist in the AllowList rule, by default, the application skips the message without scanning it.
- If the addresses are not specified in the AllowList rule, the address is checked against the denylist in the DenyList rule. If sender and recipient addresses are found in the list, by default, the application rejects the message without performing a scan. You can change the action for the DenyList rule.
If the message is not subject to global allowlists and denylists in message processing rules, the application checks if the sender address is found in personal lists of the recipient.
- If the sender address is on the personal allowlist, an Anti-Spam scan is not performed. The message is processed in accordance with the results of scanning with the other application modules.
- If the sender address is not present in the personal allowlist of the recipient, the address is checked against the personal denylist. If there's a match, the message is not delivered to the recipient who owns the personal denylist. Depending on the specified action, the application deletes or rejects the message. The application can also place the message in Backup.
* Before placing a message in Backup, the application scans the message with all protection modules. Based on the results of the scan, the application applies the strictest available action to the message. For example, if the scan results trigger a rule that applies the Delete message action but personal denylists stipulate the Reject action, the Delete message action is performed because it is the more strict response. In other words, the message is deleted in accordance with the rule settings instead of being rejected in accordance with personal denylist settings.
Messages placed in Backup are not taken into account when counting messages with the Personal denylist status in widgets in the Dashboard section.
If the addresses are not present in any of the lists either in message processing rules or in personal lists of the recipient, the message is processed in accordance with the selected rule. The rule selection algorithm is described in more detail in the chapter about the application of message processing rules.